June 24, 2010
gold coin under the hammer
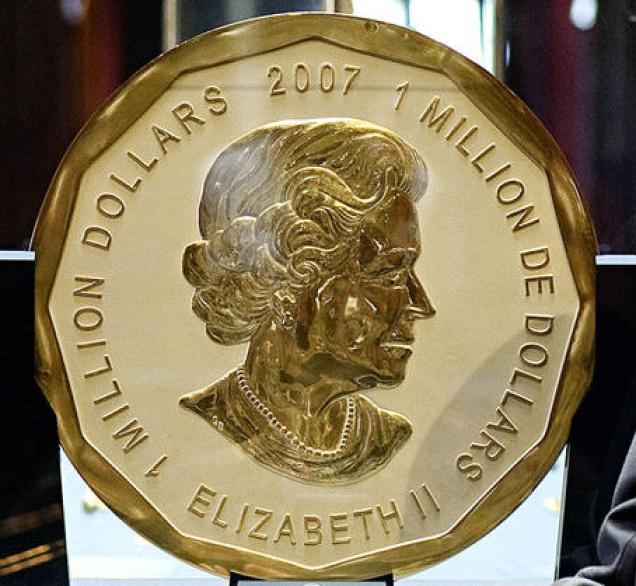
One for the gold crowd: Today one of 5 massive 100kg gold coins goes under the hammer in Vienna:
The largest gold coin in the world measuring 53 centimetres (21 inches) in diameter and weighing 100 kilograms (220 pounds) will go on sale on June 25 in Vienna, auction house Dorotheum said on Friday.The Maple Leaf coin, which is listed in the Guinness Book of World Records and carries a face value of one million Canadian dollars (800,000 euros, 970,000 dollars), was minted in Canada in 2007.
The auction price is expected to comfortably exceed the face value due to the current high price of gold. If mettled down, the gold would be worth around 3.9 million dollars (3.2 million euros).
One side of the coin carries the carries the image of Queen Elizabeth II, the official head of state of Canada, while the other side bears three maple leafs, the national symbol.
The coin was owned by Austrian investment firm AvW, which entered bankruptcy proceedings in May.
May 19, 2010
blasts from the past -- old predictions come true
Some things I've seen that match predictions from a long time back, just weren't exciting enough to merit an entire blog post, but were sufficient to blow the trumpet in orchestra:
Chris Skinner of The Finanser puts in his old post written in 1997, which says that retailers (Tesco and Sainsbury's) would make fine banks, and were angling for it. Yet:
Thirteen years later, we talk about Tesco and Virgin breaking into UK banking again.A note of caution: after thirteen years, these names have not made a dent on these markets. Will they in the next thirteen years?
Answer: in 1997, none of these brands stood a cat in hells chance of getting a banking licence. Today, Virgin and Tesco have banking licences.
Exactly. As my 1996 paper on electronic money in Europe also made somewhat clear, the regulatory approach of the times was captured by the banks, for the banks, of the banks. The intention of the 1994 directive was to stop new entrants in payments, and it did that quite well. So much so that they got walloped by the inevitable (and predicted) takeover by foreign entrants such as Paypal.
However regulators in the European Commission working groups(s) seemed not to like the result. They tried again in 2000 to open up the market, but again didn't quite realise what a barrier was, and didn't spot the clauses slipped in that killed the market. However, in 2008 they got it more right with the latest eMoney directive, which actually has a snowball's chance in hell. Banking regulations and the PSD (Payment Services Directive) also opened things up a lot, which explains why Virgin and Tesco today have their licence.
One more iteration and this might make the sector competitive...
Then, over on the Economist, an article on task markets
Over the past few years a host of fast-growing firms such as Elance, oDesk and LiveOps have begun to take advantage of the cloudtech-speak for the combination of ubiquitous fast internet connections and cheap, plentiful web-based computing powerto deliver sophisticated software that makes it easier to monitor and manage remote workers. Maynard Webb, the boss of LiveOps, which runs virtual call centres with an army of over 20,000 home workers in America, says the companys revenue exceeded $125m in 2009. He is confidently expecting a sixth year of double-digit growth this year.Although numerous online exchanges still act primarily as brokers between employers in rich countries and workers in poorer ones, the number of rich-world freelancers is growing. Gary Swart, the boss of oDesk, says the number of freelancers registered with the firm in America has risen from 28,000 at the end of 2008 to 247,000 at the end of April.
Back in 1997, I wrote about how to do task markets, and I built a system to do it as well. The system worked fine, but it lacked a couple of key external elements, so I didn't pursue it. Quite a few companies popped up over the next decade, in successive waves, and hit the same barriers.
Those elements are partly in place these days (but still partly not) so it is unsurprising that companies are getting better at it.
And, over on this blog by Eric Rescorla, he argues against rekeying in a cryptographically secure protocol:
It's IETF time again and recently I've reviewed a bunch of drafts concerned with cryptographic rekeying. In my opinion, rekeying is massively overrated, but apparently I've never bothered to comprehensively address the usual arguments.
Which I wholly concur with, as I've fought about all sorts of agility before (See H1 and H3). Rekeying is yet another sign of a designer gone mad, on par with mumbling to the moon and washing imaginary spots from hands.
The basic argument here is that rekeying is trying to maintain a clean record of security in a connection; yet this is impossible because there will always be other reasons why the thing fails. Therefore, the application must enjoy the privileges of restarting from scratch, regardless. And, rekeying can be done then, without a problem. QED. What is sad about this argument is that once you understand the architectural issues, it has far too many knock-on effects, ones that might even put you out of a job, so it isn't a *popular argument* amongst security designers.
Oh well. But it is good to see some challenging of the false gods....
An article "Why Hawks Win," examines national security, or what passes for military and geopolitical debate in Washington DC.
In fact, when we constructed a list of the biases uncovered in 40 years of psychological research, we were startled by what we found: All the biases in our list favor hawks. These psychological impulses -- only a few of which we discuss here -- incline national leaders to exaggerate the evil intentions of adversaries, to misjudge how adversaries perceive them, to be overly sanguine when hostilities start, and overly reluctant to make necessary concessions in negotiations. In short, these biases have the effect of making wars more likely to begin and more difficult to end.
It's not talking about information security, but the analysis seems to resonate. In short, it establishes a strong claim that in a market where there is insufficient information (c.f., the market for silver bullets), we will tend to fall to a FUD campaign. Our psychological biases will carry us in that direction.
September 04, 2009
Numbers: CAPTCHAs and Suicide Bombers
 Two hard numbers effecting the attack model. The cost of attacking a CAPTCHA system with people in developing regions, from the Economist's report on the state of the CAPTCHA nation:
Two hard numbers effecting the attack model. The cost of attacking a CAPTCHA system with people in developing regions, from the Economist's report on the state of the CAPTCHA nation:
The biggest flaw with all CAPTCHA systems is that they are, by definition, susceptible to attack by humans who are paid to solve them. Teams of people based in developing countries can be hired online for $3 per 1,000 CAPTCHAs solved. Several forums exist both to offer such services and parcel out jobs. But not all attackers are willing to pay even this small sum; whether it is worth doing so depends on how much revenue their activities bring in. If the benefit a spammer is getting from obtaining an e-mail account is less than $3 per 1,000, then CAPTCHA is doing a perfect job, says Dr von Ahn.
And here, outside our normal programme, is news from RAH that people pay for the privilege of being a suicide bomber:
A second analysis with Palantir uncovered more details of the Syrian networks, including profiles of their top coordinators, which led analysts to conclude there wasn't one Syrian network, but many. Analysts identified key facilitators, how much they charged people who wanted to become suicide bombers, and where many of the fighters came from. Fighters from Saudi Arabia, for example, paid the most -- $1,088 -- for the opportunity to become suicide bombers.
It's important to examine security models remote to our own, because it it gives us neutral lessons on how the economics effects the result. An odd comparison there, that number $1088 is about the value required to acquire a good-but-false set of identity documents.
July 15, 2009
trouble in PKI land
The CA and PKI business is busy this week. CAcert, a community Certification Authority, has a special general meeting to resolve the trauma of the collapse of their audit process. Depending on who you ask, my resignation as auditor was either the symptom or the cause.
In my opinion, the process wasn't working, so now I'm switching to the other side of the tracks. I'll work to get the audit done from the inside. Whether it will be faster or easier this way is difficult to say, we only get to run the experiment once.
Meanwhile, Mike Zusman and Alex Sotirov are claiming to have breached the EV green bar thing used by some higher end websites. No details available yet, it's the normal tease before a BlabHat style presentation by academics. Rumour has it that they've exploited weaknesses in the browsers. Some details emerging:
With control of the DNS for the access point, the attackers can establish their machines as men-in-the-middle, monitoring what victims logged into the access point are up to. They can let victims connect to EV SSL sites - turning the address bars green. Subsequently, they can redirect the connection to a DV SSL sessions under a certificates they have gotten illicitly, but the browser will still show the green bar.
Ah that old chestnut: if you slice your site down the middle and do security on the left and no or lesser security on the right, guess where the attacker comes in? Not the left or the right, but up the middle, between the two. He exploits the gap. Which is why elsewhere, we say "there is only one mode and it is secure."
Aside from that, this is an interesting data point. It might be considered that this is proof that the process is working (following the GP theory), or it might be proof that the process is broken (following the sleeping-dogs-lie model of security).
Although EV represents a good documentation of what the USA/Canada region (not Europe) would subscribe as "best practices," it fails in some disappointing ways. And in some ways it has made matters worse. Here's one: because the closed proprietary group CA/B Forum didn't really agree to fix the real problems, those real problems are still there. As Extended Validation has held itself up as a sort of gold standard, this means that attackers now have something fun to focus on. We all knew that SSL was sort of facade-ware in the real security game, and didn't bother to mention it. But now that the bigger CAs have bought into the marketing campaign, they'll get a steady stream of attention from academics and press.
I would guess less so from real attackers, because there are easier pickings elsewhere, but maybe I'm wrong:
"From May to June 2009 the total number of fraudulent website URLs using VeriSign SSL certificates represented 26% of all SSL certificate attacks, while the previous six months presented only a single occurrence," Raza wrote on the Symantec Security blogs.... MarkMonitor found more than 7,300 domains exploited four top U.S. and international bank brands with 16% of them registered since September 2008.
.... But in the latest spate of phishing attempts, the SSL certificates were legitimate because "they matched the URL of the fake pages that were mimicking the target brands," Raza wrote.VeriSign Inc., which sells SSL certificates, points out that SSL certificate fraud currently represents a tiny percentage of overall phishing attacks. Only two domains, and two VeriSign certificates were compromised in the attacks identified by Symantec, which targeted seven different brands.
"This activity falls well within the normal variability you would see on a very infrequent occurrence," said Tim Callan, a product marketing executive for VeriSign's SSL business unit. "If these were the results of a coin flip, with heads yielding 1 and tails yielding 0, we wouldn't be surprised to see this sequence at all, and certainly wouldn't conclude that there's any upward trend towards heads coming up on the coin."
Well, we hope that nobody's head is flipped in an unsurprising fashion....
It remains to be seen whether this makes any difference. I must admit, I check the green bar on my browser when online-banking, but annoyingly it makes me click to see who signed it. For real users, Firefox says that it is the website, and this is wrong and annoying, but Mozilla has not shown itself adept at understanding the legal and business side of security. I've heard Safari has been fixed up so probably time to try that again and report sometime.
Then, over to Germany, where a snafu with a HSM ("high security module") caused a root key to be lost (also in German). Over in the crypto lists, there are PKI opponents pointing out how this means it doesn't work, and there are PKI proponents pointing out how they should have employed better consultants. Both sides are right of course, so what to conclude?
Test runs with Germany's first-generation electronic health cards and doctors' "health professional cards" have suffered a serious setback. After the failure of a hardware security module (HSM) holding the private keys for the root Certificate Authority (root CA) for the first-generation cards, it emerged that the data had not been backed up. Consequently, if additional new cards are required for field testing, all of the cards previously produced for the tests will have to be replaced, because a new root CA will have to be generated. ... Besides its use in authentication, the root CA is also important for card withdrawal (the revocation service).
The first thing to realise was that this was a test rollout and not the real thing. So the test discovered a major weakness; in that sense it is successful, albeit highly embarrassing because it reached the press.
The second thing is the HSM issue. As we know, PKI is constructed as a hierarchy, or a tree. At the root of the tree is the root key of course. If this breaks, everything else collapses.
Hence there is a terrible fear of the root breaking. This feeds into the wishes of suppliers of high security modules, who make hardware that protect the root from being stolen. But, in this case, the HSM broke, and there was no backup. So a protection for one fear -- theft -- resulted in a vulnerability to another fear -- data loss.
A moment's thought and we realise that the HSM has to have a backup. Which has to be at least as good as the HSM. Which means we then have some rather cute conundrums, based on the Alice in Wonderland concept of having one single root except we need multiple single roots... In practice, how do we create the root inside the HSM (for security protection) and get it to another HSM (for recovery protection)?
Serious engineers and architects will be reaching for one word: BRITTLE! And so it is. Yes, it is possible to do this, but only by breaking the hierarchical principle of PKI itself. It is hard to break fundamental principles, and the result is that PKI will always be brittle, the implementations will always have contradictions that are swept under the carpet by the managers, auditors and salesmen. The PKI design is simply not real world engineering, and the only thing that keeps it going is the institutional deadly embrace of governments, standards committees, developers and security companies.
Not the market demand. But, not all has been bad in the PKI world. Actually, since the bottoming out of the dotcom collapse, certs have been on the uptake, and market demand is present albeit not anything beyond compliance-driven. Here comes a minor item of success:
VeriSign, Inc. [SNIP] today reported it has topped the 1 billion mark for daily Online Certificate Status Protocol (OCSP) checks.[SNIP] A key link in the online security chain, OCSP offers the most timely and efficient way for Web browsers to determine whether a Secure Sockets Layer (SSL) or user certificate is still valid or has been revoked. Generally, when a browser initiates an SSL session, OCSP servers receive a query to check to see if the certificate in use is valid. Likewise, when a user initiates actions such as smartcard logon, VPN access or Web authentication, OCSP servers check the validity of the user certificate that is presented. OSCP servers are operated by Certificate Authorities, and VeriSign is the world's leading Certificate Authority.
[SNIP] VeriSign is the EV SSL Certificate provider of choice for more than 10,000 Internet domain names, representing 74 percent of the entire EV SSL Certificate market worldwide.
(In the above, I've snipped the self-serving marketing and one blatant misrepresentation.)
Certificates are static statements. They can be revoked, but the old design of downloading complete lists of all revocations was not really workable (some CAs ship megabyte-sized lists). We now have a new thing whereby if you are in possession of a certificate, you can do an online check of its status, called OCSP.
The fundamental problem with this, and the reason why it took the industry so long to get around to making revocation a real-time thing, is that once you have that architecture in place, you no longer need certificates. If you know the website, you simply go to a trusted provider and get the public key. The problem with this approach is that it doesn't allow the CA business to sell certificates to web site owners. As it lacks any business model for CAs, the CAs will fight it tooth & nail.
Just another conundrum from the office of security Kafkaism.
Here's another one, this time from the world of code signing. The idea is that updates and plugins can be sent to you with a digital signature. This means variously that the code is good and won't hurt you, or someone knows who the attacker is, and you can't hurt him. Whatever it means, developers put great store in the apparent ability of the digital signature to protect themselves from something or other.
But it doesn't work with Blackberry users. Allegedly, a Blackberry provider sent a signed code update to all users in United Arab Emirates:
Yesterday it was reported by various media outlets that a recent BlackBerry software update from Etisalat (a UAE-based carrier) contained spyware that would intercept emails and text messages and send copies to a central Etisalat server. We decided to take a look to find out more....
Whenever a message is received on the device, the Recv class first inspects it to determine if it contains an embedded command more on this later. If not, it UTF-8 encodes the message, GZIPs it, AES encrypts it using a static key (EtisalatIsAProviderForBlackBerry), and Base64 encodes the result. It then adds this bundle to a transmit queue. The main app polls this queue every five seconds using a Timer, and when there are items in the queue to transmit, it calls this function to forward the message to a hardcoded server via HTTP (see below). The call to http.sendData() simply constructs the POST request and sends it over the wire with the proper headers.
Oops! A signed spyware from the provider that copies all your private email and sends it to a server. Sounds simple, but there's a gotcha...
The most alarming part about this whole situation is that people only noticed the malware because it was draining their batteries. The server receiving the initial registration packets (i.e. Here I am, software is installed!) got overloaded. Devices kept trying to connect every five seconds to empty the outbound message queue, thereby causing a battery drain. Some people were reporting on official BlackBerry forums that their batteries were being depleted from full charge in as little as half an hour.
So, even though the spyware provider had a way to turn it on and off:
It doesnt seem to execute arbitrary commands, just packages up device information such as IMEI, IMSI, phone number, etc. and sends it back to the central server, the same way it does for received messages. It also provides a way to remotely enable/disable the spyware itself using the commands start and stop.
There was something wrong with the design, and everyone's blackberry went mad. Two points: if you want to spy on your own customers, be careful, and test it. Get quality engineers on to that part, because you are perverting a brittle design, and that is tricky stuff.
Second point. If you want to control a large portion of the population who has these devices, the centralised hierarchy of PKI and its one root to bind them all principle would seem to be perfectly designed. Nobody can control it except the center, which puts you in charge. In this case, the center can use its powerful code-signing abilities to deliver whatever you trust to it. (You trust what it tells you to trust, of course.)
Which has led some wits to label the CAs as centralised vulnerability partners. Which is odd, because some organisations that should know better than to outsource the keys to their security continue to do so.
But who cares, as long as the work flows for the consultants, the committees, the HSM providers and the CAs?
June 11, 2009
another implausible reason to steal from iTunes?
I haven't been blogging much, because for the most part there isn't much that is new to say. I generally blog for my own reasons, like getting complex thoughts into a cohesive written form, as a discipline in reducing the crud.
But sometimes the yearning comes back. Here's a funny one about iTunes:
Gang arrested for buying own music online with stolen cards UK police have arrested nine people accused of using stolen credit cards to buy music they made themselves from iTunes and Amazon, fraudulently netting around $300,000 in royalties.The gang is accused of creating several songs before using an online US company to upload them to Amazon and iTunes for sale.
Between September 2008 and January 2009 the group allegedly used around 1500 stolen or cloned British and American credit cards to buy $750,000 worth of songs.
Apple and Amazon, who at the time were unaware of the plot against them, paid royalties totalling $300,000 out on the sales.
OK, that's funny. On first blush it looks like a good way to launder the funds from stolen credit cards. The problem of course is that it leads back to the perpetrators, in a very strange and "sore thumb" way.
When all these stolen credit cards start showing a high iTunes pattern, the logic is pretty easy to follow. Does a crook need to buy a song on iTunes? No, a crook has easier ways like cracking it or downloading it from any of a dozen open sites. So they don't want the song ... so follow the money. Which is easy to do with a bit of datamining software.
With slightly more thought, then, this reveals a rather stupid bunch of crooks. What do we do when we catch a rather stupid bunch of crooks? Not much, because they will eliminate themselves one day or other from something else. Therefore this is nothing more than a funny story.
January 30, 2009
Brit Frauds, the Bezzle, and Signs of Rebellion in Heartland
Payments fraud seems up in Britain:
Matters found that around 26% fell victim to card fraudsters in 2008, up five per cent on the previous year.Kerry D'Souza, card fraud expert, CPP, says: "The dramatic increase in card fraud shows no sign of abating which isn't surprising given the desperate measures some people will resort to during the recession."
The average sum fraudulently transacted is over £650, with one in 20 victims reporting losses of over £2000. Yet 42% of victims did not know about these transactions and only found out they had been defrauded when alerted by their bank.
Online fraud affected 39% of victims, while card cloning from a cash point or chip and pin device accounted for a fifth of cases. Out of all cards that are physically lost and stolen, one in ten are also being used fraudulently.
One in 4 sounds quite high. That's a lot higher than one would expect. So either fraud has been running high and only now are better figures available, or it is growing? They say it is growing.
While researching origins of failure I came across this interesting snippet the other day from Richard Veryard:
The economist J.K Gailbraith used the term "bezzle" to denote the amount of money siphoned (or "embezzled") from the system. In good times, he remarked, the bezzle rises sharply, because everyone feels good and nobody notices. "In [economic] depression, all this is reversed. Money is watched with a narrow, suspicious eye. The man who handles it is assumed to be dishonest until he proves himself otherwise. Audits are penetrating and meticulous. Commercial morality is enormously improved. The bezzle shrinks." [Galbraith, The Great Crash 1929]
If this is true, then likely people will be waking up and demanding more from the payments infrastructure. No more easy money for them. Signs of this were spotted by Lynn:
"Up to this point, there has been no information sharing, thus empowering cyber criminals to use the same or slightly modified techniques over and over again. I believe that had we known the details about previous intrusions, we might have found and prevented the problem we learned of last week."Heartland's goal is to turn this event into something positive for the public, the financial institutions which issue credit/debit cards and payments processors.
Carr concluded, "Just as the Tylenol(R) crisis engendered a whole new packaging standard, our aspiration is to use this recent breach incident to help the payments industry find ways to protect its data - and therefore businesses and consumers - much more effectively."
For the past year, Carr has been a strong advocate for industry adoption of end-to-end encryption - which protects data at rest as well as data in motion - as an improved and safer standard of payments security. While he believes this technology does not wholly exist on any payments platform today, Heartland has been working to develop this solution and is more committed than ever to deploying it as quickly as possible.
Now, if you've read Lynn's rants on naked transactions, you will know exactly what this person is asking for. And you might even have a fair stab at why the payment providers denied Heartland that protection.
January 22, 2009
Skype: the gloss is losing its shine
Skype loses some of its shine. Here's a list I've built up over the last year, others have better lists.
- the Chinese use it for targetting and eavesdropping.
- In other rumours, it has been said (!) that the intel agencies can now break in to Skype. But there is no confirmation of this.
- Recall that Skype is now owned by eBay, which is probably the biggest signal of all.
- More woes reported by Economist.
- The taliban use it, and it is devlish difficult to crack, so say the tommies.
- Meanwhile, a released open source intel document on terrorist tools is strangely discrete about it. Probably distracted by all the other things like twitter terrorist attacks and mobile cameras in missiles...
- Confirming that intelligence ho-humedry, the Mumbai terrorists used a big array of tech tools, some of them completely compromised, and the tools were even intercepted! They still got their job done, allegedly or apparently or by some measures. Maybe the genie is really out of the bottle, and no amount of cracking Skype will slow down the revolution for the committed do-badder? Or maybe the Internet and telecommunications has reached the commoditisation stage where it is just like clothing, and even terrorists are adept at wearing t-shirts and jeans and iPods.
- this very nice resource: http://www1.cs.columbia.edu/~salman/skype/.
- And, hot off the press is today's news: here is evidence that Skype is scanning your other applications for purposes evil and nefarious (also encrypted in French). Who's to blame here? Skype for getting over-eager to sell your identity, or Firefox for not protecting the user from the compromise platform? Actually, the latter looks pretty guilty of naivete here, the platform as attacker has been on the validated threat list for how long now? Again, Skype leads the way by carefully protecting *itself* from other client-attacks (good use of RC4, that!). Which in no way absolves Skype of the crime of reading data from other applications. If true, that's a class-action lawsuit for eBay, and they'd better have some good answers.
Summary?
- Skype is still the single best system out there for your privacy.
- In terms of points, it beats any other system, hands-down.
- But the cracks are showing, the shine is off the new factory paint job.
- Any day now, I expect that confirmation will turn up that they screwed up your privacy in one way or another.
- Still, it also remains the bright shining light of security architecture. For that alone it is worth following.
This is inevitable. All great revolutions start out from perfect motives and morals, which then get trashed. Meet the new boss, same as the old boss. There is no doubt that Skype cannot provide the permanent libertarian wet-dream of defeating governments and crooks forever. Intel agencies will eventually get in, crooks will find a way, its new owner will put pressure on the company to monetarise the investment, and you the user will be screwed as always.
Enjoy the bounty while it lasts.
Tossing the phone
Oct 10th 2008
From Economist.com
Though a great alternative, Skype is open to abuse
LATE last year, your correspondent decided he was paying too much for long-distance telephone calls, and vowed to switch to one of the new VOIP (voice over internet protocol) services, which offer calls to most places in the world for a few pennies a minute at most. At the time, his land-line carrier (Verizon) was charging him five cents a minute for local calls, 11 cents for long-distance, and around 16 cents for international calls. With lots of contacts in Britain and Japan, over half his monthly phone bill was for international calls.
Many PC users got their first taste of VOIP in the 1990s when a product called VocalTec first hit the market. But because of the technical hassles involved, making calls between two PCs connected to the internet wasnt for the faint of heart.
Skype changed all that in 2003 with a delightfully simple piece of software that could be downloaded for free and used to talk to other Skype users around the world with no charge whatsoever. Since then, close to 300m copies of the Skype software have been downloaded, and 13m Skypers are jabbering away cheerfully on any given day.
Reuters
You can still use Skype to talk to other users around the world for free. Thats a terrific dealprovided, that is, the person youre contacting is sat at a computer.
But what if you want to reach someones land-line or mobile number? No problem. Either buy Skype credit online and pay around two to three cents a minute, or purchase a monthly subscription for $9.95 and make unlimited calls to other peoples phones anywhere in the world.
Best of all, Skype offers video and text-messaging as well as good old-fashioned talk. Your correspondent first started using Skypes video-conferencing feature in 2006 when working for several months in Japan. He found it an ideal way to help his nine-year-old with her homework.
With so much going for it, Skype has attracted its share of wannabes. Before deciding to hang up his land-line, your correspondent investigated a number of Skype alternativesincluding SightSpeed and Gizmo Project (now Gizmo5) as well as newcomers like Mobivox, iSkoot, TalkPlus, Jajah and Jangl. With a few honourable exceptions, most looked financially fragile and have subsequently had trouble turning their technologies into worthy contenders.
Two things made Skype the obvious choice. One, of course, was its ease of use, especially its video-conferencing facility. Improvements in video qualityalong with the capacity for full-screen video plus picture-in-picture in the latest versionshave made using Skype only more compelling.
The other clincher was the way the Skype software also runs on dozens of mobile phones as well as game consoles and other internet appliances. Your correspondent currently uses a dedicated Skype phone that automatically logs on to any open Wi-Fi network within hailing distancelike a smart phone with a built-in Wi-Fi radio as well as a cellular connection. Open Wi-Fi hotspots are ten-a-penny in coastal California.
Though it has saved him several thousand dollars over the past six months, your correspondent finds Skype to be not without its problems. In particular, the more he uses it, the more he worries about its lack of security.
Sure, Skype relies on some of the best encryption technology around to prevent ordinary eavesdroppers from listening in to conversations. For a start, the users login is certified by the widely-trusted RSA algorithm. And the information being transmittedwhether voice, video, text or computer datais scrambled with the same 256-bit AES encryption method used by the military everywhere.
But because Skype sends and receives calls with a proprietary protocol that is closely guarded as a company secret, theres no way of knowing how tamper-proof the network really is. There could even be a backdoor to the software, of which the people at Skype itself might be unaware. When a network provider says, effectively, Trust useverythings fine, you would have to be naive not to have at least some reservations.
Thats an even greater concern when you know that anyone can join the network without having to prove his identity. The fact is, users can set up any number of Skype accounts, each under a different fictitious name, and never be challenged. In short, this is not the telephone system that Ma Bell made a model of trustworthiness and reliability. Skypers are out there in the big, bad world at its ugly worst.
You can see why Skype terrifies IT managers particularly. Because it was designed by the same bright sparks in Estonia who created the virtually unstoppable KaZaA file-sharing networkand it uses much the same proprietary form of peer-to-peer architectureSkype can evade practically every firewall known to man.
With messages bounced from one users computer unknowingly to anothers before reaching their final destination, there is no central server directing the traffic flow, logging the calls, and screening them for viruses, Trojan horses and spyware.
In short, its a perfect vehicle for delivering malware to the inner sanctum of any organisation, as well as sneaking corporate secrets out. Such features hardly can escape the attention of those criminals who surreptitiously commandeer hordes of innocent users computers to launch devastating botnet attacks on organisations.
Then theres a little matter of compliance. Because of its heavy encryption, firms have no way of recording Skypes voice and video calls to meet their financial and legal obligations under the Sarbanes-Oxley Act. That alone can leave them wide open to criminal penalties.
If thats not enough for IT managers as well as individual users to worry about, the blogosphere has lately been abuzz about the way Skype tracks every computers identityand quite possibly its whereabouts.
Civil-liberties folks are concerned that this could provide a powerful tool for authoritarian regimes to keep tabs on annoying dissidents. Skype, you may recall, got a black eye for helping the Chinese authorities filter conversations for sensitive words like democracy, independence, earthquake and more recently melamine.
Unless you are running the 64-bit version of Windows, youll never notice a tiny file called 1.com that Skype launches when its users log on. This tiny 16-bit program (which Windows 64 cant read and therefore reports as an error) executes in a flash and unloads itself immediatelybut not before reporting back the identity of the computers motherboard.
If you were so inclined, correlating a computers ID with its internet address would make tracking the movement of anyone using Skype a doddle.
Mischievously, your correspondent has sprinkled empty 1.com files throughout his Windows directoryto see whether denying Skype the chance to interrogate his computers identity triggers any disruptions. So far, nothing untoward has happened. He would be amused to hear from readers who have taken similar precautions.
August 13, 2008
Silver bullets, silver homers
Some things that have been disturbing my desktop for too long. First, a silver bullet spotted:
Verisign Aims to Deflate 'Pump and Dump' Scams August 11, 2008 By David Needle.A fraud-detection service warns online brokerages when they're about to make a trade that looks fishy. Verisign is taking a new approach to the battle against so-called "pump and dump" schemes that artificially hype stocks.
A new module for the company's VIP Fraud Detection Service, set for release this Friday, features a "self-learning" behavioral engine designed to help brokerages spot and avoid pump and dump activity. The system works by weighing a number of factors, including stock risk, user behaviors, how trading compares to known fraudulent trades and the volume of trading for a particular stock.
The notion that a broker has to be told what is a dodgy stock and what is a scam is a bit like telling a mafiosa what is a crime, or the pope what is a heathen.
 Meanwhile, over in Euro-coin-land:
Meanwhile, over in Euro-coin-land:
A one euro coin has turned up in Spain bearing the face of cartoon couch potato Homer Simpson instead of that of the country's king, a sweetshop owner told Reuters on Friday.Jose Martinez was counting the cash in his till in the city of Aviles, northern Spain, when he came across the coin where Homer's bald head, big eyes and big nose had replaced the serious features of King Juan Carlos.
"The coin must have been done by a professional, the work is impressive," he told Reuters.
In the old days, the punishment for forging money was to lose ones head, so we expect Homer to be arrested any day now.
I'm guessing that some artist has done this, and only after they did it did they find out how many years of jail they are facing.
 Question is, does the artist's right override the right of the Seignor to collect his seigniorage? Given the record of central banks lately, the latter's right is looking increasingly dodgy.
Question is, does the artist's right override the right of the Seignor to collect his seigniorage? Given the record of central banks lately, the latter's right is looking increasingly dodgy.
December 29, 2007
2008 -- The Year of the Raven!
What lies in store for us next year?
- More security gloom. There has to be a turn-around in process to make it stop going down, or fraud has to reach an economic limit or balance. Neither is yet in sight. So, no change: fraud up. Gloom up. Panic up. Only thing down is confidence, faith and the already tattered reputation of the security industry.
- Lies and deception are an issue. It's routine in business it seems, and it is a fascinating game theory question why this has become prevalent.
"Well, if they want to try to manipulate, I can play that game too. [I] gave every known body signal there is telling of lies ... covered my mouth, scratched my elbow, looked away and so on."
At the notable DigitalIdForum.com in London, I heard one statistic that stuck out: the correlation between CVs and capabilities is 0.3, in Britain at least. For those who forget their statistics, this puts the Curriculum Vitae closer to rubbish (0.0) than to value (1.0). Look for the correlation to turn negative, and we'll all have to play the game of guessing which employee skills are precisely the reverse...
Seriously though, the CV is the core tool in the search for jobs; what does that tell you about the employment industry? And what does that tell you about the employees that you already have?
My prediction for the year to come: more attention to just why deception and lies are so much a part of our business relationships. I therefore dub this the Year of the Raven, although the real reasons for this are too deceptive to be revealed.
- Last year, we saw the realisation that the security profession was in the problem space, not the solution space. I predict there will be some soul-searching in the academic world as well. How many papers have you read this year that fail to come close to the problem space, let alone the solution space? Some of them are just plain case studies in what's wrong with academia.
- Bad news for the academic credibility of security conferences, but good news for their attendance. Good news for related fields, and indeed there will be a rush to introduce other things.
There will be more attention on psychology (I saw an excellent presentation on the psychology of deception at DigitalIdForum. Did you know that adults deceive around twice per day? Tricked again, dammit!). Also, economics is in full fashion, alongside user interface and usability studies. In around 2 years, I predict that people will start to think of Open Governance, and end up discovering where FC was 10 years ago. Or could have been.
- Mozilla created a new business framework around the Thunderbird email client. This might pay dividends if it creates the incentives to add some usability to the thing they call S/MIME. Or maybe not, we'll see. This could be good, as the potential to turn Thunderbird into a viral security agent for the user is definately there, but it does require some opportunistic thinking. It has all the code in it, just a woefully old and tired security model that should have been trashed the day after Christmas of 1994, like all the other toys from the 1970s.
- Europe is in the early skirmishing phase of a "war on cash." Expect a cassus belli sometime in 2008. Like all wars these days, it is totally bogus. In this case, it can been seen as simply another request for another subsidy from the banks, or more complexly, an exchange of the SEPA political favour for the monopoly payments franchise.
So far, the competition people in the EU haven't worked it out, and the central banks and other "payments authorities" are tripping over themselves to present the "costs of cash" with no thought as to the "cost of bank subsidies." As always, the people will lose this war, but at least it is limited to the European peoples.
- Macs will still be the better alternative for security for another year. The cracks are showing, and some attacks will bite, but in the pure comparison sense, it still makes sense to buy a Mac. Expect a few actual breaches and viruses, etc, and much trumpetting of how Macs are insecure. Don't be fooled, it takes more than a year to get from 0% of windows insecurity to 100%.
- As predicted last year, Vista failed to make the difference. This means that Microsoft has given it their best shot, and failed. So they now have to think out of the box and make major structural changes to the model. Which means: rewrite the OS. Look for signs of operating systems research, on both how to do it, and what's available to snaffle. Normally Microsoft would not pick up other people's work in such a sensitive area, but this time it's different, *iff* there is anything that will help. Anyone got a caps OS handy?
- OLPC could not have picked a better time. Their new OS (with caps and all that good stuff in it) will inspire many of the research / geek sector, and therefore we predict it will become a credible alternative to the OS menu (at least as credible as Minix and the experimental linuxii, etc, and more credible than Next, etc). We might not know for 5 years whether it will storm the barricades, but this year will see its steady rise.
- Which means we are seeing the slow but steady regularisation of the OS market. Once it was just MS Windows. Slowly, Unix is clawing back, with Mac and with Linux. Unlike with the CPU market which saw the dramatic turnaround from monster to duopoly over the only 4 years, this will be slow. Watch for signs of increasing annoyance from PC sellers and switching to non-MS-installed sales.
- News in pure FC is likely to be pretty much limited. Again, complexity slows it down, so it is the same old story: great opportunities are missed because the people who are doing them have ignored all the academic advice (good) and thus lose the big picture (bad).
- Don't expect much change in the Certificate Authority world. EV succeeded so Verisign++ is further entrenched. CAcert continues to prove the pros & cons of an open source organisation: it is easier for the open source world to create a broad techie organisation than a deeply governed organisation. Because of audit impositions, the old bazaar trick that worked for Linux, Mozilla, Apache, the BSDs, etc, just doesn't work for CAs.
However, the fundamentals are still good for an open CA, so we'll plough on. Prediction: by the end of 2008 we'll know whether CAcert can make it or not as a serious CA, and whether there is any hope for the browser/email security models to start delivering crypto to the users. (Audit-wise, that is, being the only language that matters to the big vendors.)
- Online banking still lurches along, caught in the trap of user-confidence and an inability to deploy another channel. The result of course is user deception, self-deception and more losses. As there are no competitive forces in sight to inspire some change, we are looking at a slow race developing between attackers and the banks, where both will be counting the losses on both sides of their balance sheets. The only comprehensive loser is again, the user.
- e-gold will likely have to be restructured over the next year. So many blows, so much loss of confidence; still, my record of predictions with e-gold is not good so I'll refrain from further speculation. WebMoney and Goldmoney should have a good year, and as they are in different application spaces, they'll not bump head to head.
- the blog will remain quiet, partly because a lot of the interesting stuff has already been written, and partly because at least one blog (Dave's digital money) now covers a lot more of the classical fc news & views.
The formula for a popular blog has also affronted: lots of lightweight posts, many divergent authors, stick to something everyone can happily disagree with, make it part of a spectrum of marketing, not a lone voice. Has the blog craze run its course? I think so, but the replacement isn't clear (podcasts have been tried, but they don't appeal. Video is ok for mass market, but it is more costly to make the grade in the serious market).

Enough is enough! Enjoy your year, and even if you find your industry in turmoil, try and create the sense of space needed to reflect on the real things that went wrong. The good news is that we rarely get to live in interesting times, the bad news is that there will be 100 opinions on why, and only a statistically insignificant portion of them will be close. So sayeth the Raven!
December 15, 2007
2007: year in review...
So what happened in 2007? All doom and gloom, really. Here's a roundup of what I called the year of the platypus, for some mixed up reason to do with security in its own worse nightmare:
- Security went down, overall. Net Fraud went up, overall. Breaches kept on being reported. Software author liability was discussed. In other words, no news.
- One bright spot is that it is now considered wisdom that the security profession and/or industry has failed. I first wrote about the hypothesis of failure in mid-2004, and at that time, phishing, breaching and other industrial-scale crimes were considered ignorable problems. (I don't think I was necessarily the first, but perhaps the most outrageous.)
For this reason, I dubbed 2007 the year of the platypus. During that year, all of the major security commentators clicked into consensus on this hypothesis. This is good. Before, it was impossible to fix because all efforts at security amounted to the old medical practice of wrapping up battle wounds in bandages and not taking them off until the limb fell off. Now that those in the security field include themselves in the problem space, rather than the solution space, there is some hope to at least understand the spaces.
- My suggestion that every CSO needs an MBA went down like a lead balloon. Possibly because nobody fully groks the signal-economics of the CISPP, et al, and thus they are hardly capable of accepting a qualification that claims as its plus points nothing to do with security, an order-of-magnitude cost increase over popular alternatives, and, worse of all, you have to really work for it. No good can come of that! And to be fair, Spencian mathematics predict that this won't work in the Alice-in-wonderland world of signalling, because additional value-added is ignored beyond a minimum point that achieves stability in the market for silver bullets.
- OpenPGP went to RFC4880, after ten years of delay. In one sense this means little as those who don't use OpenPGP are not going to change, and those who do won't worry. In another sense, because it means that OpenPGP is now as solid ("got a standard") as its erstwhile PKI cousin(s), we can more clearly discuss a better model. Which helps, because it is the only infrastructure that is useful, economic and net-scaleable for human signing.
- The UK got a rude awakening, firstly when the government disagreed with the entire security industry's best efforts (Her Majesty's ministers are avid readers of FC?) and then when the self-same government lost its database. British security pundits are fleeing in droves down to their local comedy house, where they'll get more respect as stand-up comedians.
- Stormbot surged across the top of beyond to become the biggest threat to the popular mind since the Blight. I reported (with some level of respect) that this signalled a new phase: the arisal of a serious criminal mastermind, Moriarty-like, or better known as the systems architect in computing lingo.
Others reported with life-threatening degrees of hyperventilation how Stormbot swarmed into computer researchers minds and initiated fear and panic. Next, we'll be telling crypto-jokes about the fall of RSA. (These images brought to the nyour mind, courtesy of the Blight, from _A Fire Upon the Deep_. Death to Vermin.)
- I predicted that this year, Vista would fail to make a difference to the security game. Which leads to a need to redesign from scratch. Bruce Schneier thought so too:
Redesigning the Microsoft Windows operating system would work, but that's ridiculous to even suggest.
Or maybe not. Vista failed to make a diffference, so the logical conclusion is also the ridiculous one, to paraphrase Sherlock Holmes. I guess we'll see next year :)
- As predicted, Apple Macs enjoyed a year of protecting their users. So did Firefox.
- Practically zero news from Cardspace/Info???. This is a worry. Regardless of ones depressed feelings of another Microsoft security initiative, there were some good seeds sown in that design.
- All trust of any form was lost in the American government (called there "the administration"). So much so that they started pushing for reform on global warming. Where this leaves us in the FC field is counting the damage done to the governance of the spooks and cops. That might take decades, as a lot of the stuff was secret.
- In payments news, the e-gold guys got indicted, following a run of "brushes with the law". That was the end of an era, and sparked some sadness; it could have been different. In the end, it has made things much harder for the rest of the players as they now have deal with the overbearing and dirty image. Yet another innovation in finance has been sacrificed to ego, and we the people will lose another decade or two in getting competitive payments systems.
- In further and more serious payment news, the telco fascination took deep hold in the subconsciousness of many observers. No longer just the fantastical prediction (the Trotter observation of 1998), telcos are predicted to be the owner of the wave of the future of payments. Not so fast, I say: like banks, telcos are not stellar in the understanding of this field, and there is still plenty of room for the extraordinary losses, film-story bungles and outrageous claims.
- Curiously, gift cards and small issuers and the like slipped out of the observer's consciousness. (Curious here means, I predicted otherwise, and was wrong...) Rumour has it that the EU has decided to kill the digital money directive. Perhaps an act of kindness, as the banks made sure the thing was born crippled and insane from the beginning? And, it's ok because the EU still has SEPA, the mandated response to the failure in competition? Right?
- Small FC challengers such as zopa.com fight on, under the yes-it's-meant-to-kill-you suffocating blanket of regulation. Second Life lurches along, much like Paypal days of old; if it survives as a financial system it will be because of brutal survival skills. WebMoney continues to inhabit the spot of "the one I'd worry about if I was you."
- Open source established itself further as the credible alternate. It is now routine for groups I deal with to use Firefox, Thunderbird and share documents using OpenOffice. No matter how sensible that is... Mac share still grows in the meetings I go to, and I am beginning to be suspicious of claimed market share numbers.
- From the monetary economics department, the collapse of the US dollar was well established. Finally, the imbalance that started around 2000 became accepted as policy not anomaly. News from the underground indicated that Sir Alan initiated the process of dealing with the massive shift in value in 2003, but it took until this year that the mainstream realised that falling dollar prices signalled a long term shift based on the rise of the Euro, over-expenditure of the USG and a few petro-wars thrown in to provide a colourful backdrop.
- The big question that was on everyone's mind was finally answered: what happens when the world currency gets out of balance? meltdown? panic? blood in the streets? the answer was of course more simple and more sinister: the other central banks took half the value on the table. That is, where gold was indicating a 2-3 fold value collapse, Euros, Sterling, Aussies and others inflated their currencies in between the squeeze. Thus, housing booms maintained, currencies appreciated, and economic records maintained intact. But behind the mirrors, another story unfolds...
- The blog went quiet. Partly, it was because there was little or no news. Partly because I got more involved in the great certificates adventure.
- Predictions I got wildly wrong: AES stands strong, but I will say that 128 should be avoided. EV seems to have won out when Mozilla decided to add it, which probably will force the arisal of the two tier market (no bad thing in marketing terms but not a comfortable result, if you know what I mean).
Well, that's enough for me, and probably more than enough for any sane person! Enjoy Xmas, and maybe we can conjure up something better for the new year.
January 11, 2007
Pennies - RSA reveals attack kits? and Why Gift Cards,
From Epayment news:
Jan 11 2007 : RSA Security says it has discovered a phishing toolkit which is being sold on Internet fraudster forums. The so-called "universal man-in-the-middle phishing kit" enables sophisticated "next-generation" attacks against banks and e-commerce sites, the U.S. Internet security firm says.
Funny, that's more or less what we reported nearly a year ago.
Someone reveals one of the insider secrets about Gift Cards:
According to the research from TowerGroup, consumers purchased $80 billion worth of gift cards in 2006. Of that, $8 billion will never be redeemed.
Yup. Hard numbers though, and I suspect the figure is higher.
Also, a couple of hollywood-file-sharer love-in notes:
Leslie Moonves, president of CBS Corp., and Robert Iger, chef executive of The Walt Disney Co. both gave keynote addresses this year that emphasized cooperation between studios and device makers."If you asked me two years ago, did I want Disney in the keynote? No," said Gary Shapiro, chief executive of the Consumer Electronics Association, annual sponsor of the CES show. "Disney was the poster child in Washington for the most anti-technology company there was."
May 05, 2006
Security Soap Opera - (Central) banks don't (want to) know, MS prefers Brand X, airlines selling your identity, first transaction trojan
Journalist Roger Grimes did some research on trojans and came up with this:
Even more disturbing is that most banks and regulatory officials dont understand the new threat, and when presented with it, hesitate to offer anything but the same old advice.Every bank and regulatory official contacted for this article said they have already recommended banks implement a two-factor or multifactor log-on authentication screen. In general, they expressed frustration at the amount of effort it has taken to get banks to follow that advice. And all complained about the trouble these schemes are causing legitimate customers.
When told how SSL-evading Trojans can bypass any authentication mechanism, most offered up additional ineffective authentication as a solution. When convinced by additional discussion that the problem could be solved only by fixing transactional authorization, most shrugged their shoulders and said they would remain under pressure to continue implementing authentication-only solutions.
They were also hesitant to broach the subject with senior management. It had taken so long to get banks to agree to two-factor authentication, they said, it would be almost impossible to change recommendations midstream. That puts the banking industry on a collision course with escalating attacks.
On the nail. (Sorry, Dave!)
Microsoft has apparently expressed a preference of smart cards over two-factor tokens:
More interesting is Microsoft's long-term view of two-factor authentication. In contrast to companies such as E*Trade, AOL, and VeriSign which have either announced support for or are already supporting one-time password + security token combinations for their customers, Microsoft sees things moving in a different direction, according to a spokesperson.Most customers told Microsoft they do not view one-time passwords as strategic and are looking long term to smart cards as their preferred strong authentication mechanism.
In any soap opera, there appear advert breaks where the housewife is offered the choice of bland brand A versus bland brand B. "Most housewifes we surveyed chose Brand X soap powder." Maybe Microsoft's heart is in the right place, though:
Last week, Microsoft pledged to bring about 100 legal actions against phishers in Europe, the Middle East and Africa (EMEA) over the next few months.
That's smart. Given their risk exposure, they'd better have something good to bring to the negotiating table, especially given their extensive experience in prosecuting evil software copiers and less extensive success in stopping spam. To take a leaf out of Chandler's book, with fraud you are either fighting them or your are supporting them. (hmmm, spoke too soon.)
Adam finds an article on how Adam Laurie and Steve Boggan "hacked" the airline ticket tracking systems to extract the full identity of a flyer. Skipping the details on the hack itself (did buying the ticket establish their credentials?) the piece is more relevant for its revelations of just how much data is being put together for erstwhile tracking purposes.
We logged on to the BA website, bought a ticket in Broer's name and then, using the frequent flyer number on his boarding pass stub, without typing in a password, were given full access to all his personal details - including his passport number, the date it expired, his nationality (he is Dutch, living in the UK) and his date of birth. The system even allowed us to change the information.Using this information and surfing publicly available databases, we were able - within 15 minutes - to find out where Broer lived, who lived there with him, where he worked, which universities he had attended and even how much his house was worth when he bought it two years ago.
The article talks about how the Europeans handed over the data to the Americans in apparent breach of their own privacy rules. Things like what means you ordered, what sort of hotel room. Today you're a terrorist for ordering the ethnic meal, and tomorrow you run the same risk if you swap hotels and your hotel chain doesn't approve. Think that's extreme? Look how the information creep has started:
"They want to extend the advance passenger information system [APIS] to include data on where passengers are going and where they are staying because of concerns over plagues," he says. "For example, if bird flu breaks out, they want to know where all the foreign travellers are.
That's nothing more than an excuse by the system operators to extract more information. Of course, your hotel will be then required to provide up to date information as to where you moved next.
A data point - perhaps the first transaction trojan. FTR:
Transaction-based SSL-evading Trojans are the most dangerous and sophisticated. They wait until the user has successfully authenticated at the banks Web site, eliminating the need to bypass or capture authentication information. The Trojan then manipulates the underlying transaction, so that what the user thinks is happening is different from whats actually transpiring on the sites servers.The Win32.Grams E-gold Trojan, spawned in November 2004, is a prime example of transaction-based type. When the user successfully authenticates, the Trojan opens a hidden browser window, reads the users account balance, and creates another hidden window that initiates a secret transfer. The users account balance, minus a small amount (to bypass any automatic warnings), is then sent to a predefined payee.
Many SSL-evading Trojans are one-offs, meaning that they are encrypted or packaged so that each Trojan is unique -- defeating signature-style detection by anti-virus software.
Ultimately, SSL-evading Trojans can be defeated only when users stop running untrusted code -- or better still, when banks deploy back-end defensive mechanisms that move beyond mere authentication protection.
Sorry about the "blame the user" trick at the end. When will they ever learn?
April 22, 2006
News and Views - Mozo, Elliptics, eBay + fraud, naïve use of TLS and/or tokens...
Firefox, the free open-source Web browser from Mozilla Corp., quietly gained enough users in March to finally grab 10% of the Web browser market, according to a report released yesterday by Web audience-measurement firm NetApplications.com.
Funny, I thought that happened long ago.... On the even better news front, Frank Hecker is now posting weekly diaries of action at the Mozilla Foundation. This is an excellent idea, as they are stuck between a rock and a hard place - a non-profit with lots of money and no obvious way to govern it. Here's a snippet of some relevance to FC but the real news is that Mozilla do seem to be taking the search for governance seriously. A snippet:
PKI R&D Workshop. I attended the PKI R&D Workshop at NIST in Gaithersburg MD, and participated on a panel discussion on browser security. Note also that Bob Relyea of Red Hat spoke about work by Red Hat and Sun to support elliptic curve cryptography in the NSS crypto library and hence in Firefox and other Mozilla-based products, as well as in server products from Red Hat and Sun. For more information see Bob's presentation; the rest of the workshop presentations and papers are also available online.
Presumably Red Hat and Sun are interested in supporting the NIST Suite B because of potential USG sales. It will be interesting to watch how this falls out - will the endorsement of NIST (and in the background, the NSA) push elliptic curve cryptography forward to adoption? Or will the patent free (and therefore cheap) alternatives we already have maintain their open dominance?
A great post by Cubicle on fraud over at eBay. He talks about how the company has drifted and postured to the point where they are now providing infrastructural support for scammers - because it is the scammers that pay their fees.
The mere existence of Second Chance is interesting because it indicates to me that ebay has significant enough outtrade and settlement risk issues that theyre losing a significant number of sellers, so theyve created Second Chance as a mechanism to help sellers better mitigate settlement risk. Unfortunately, theyve tilted the balance in favor of unscrupulous sellers in the process.Look at the risks of Shill Bidding from the sellers perspective. If they get too greedy, they will exceed the limit of their bidders and wind up winning their own auction. This costs them whatever the listing fee on the item was and they still have to re-list (and re-pay the fee), doubling their transaction cost and hope that they dont overbid the auction again.
Now, thanks to Second Chance, ebay has effectively provided a safeguard which mitigates the risk to a greedy seller of exceeding the buyers maximum price. The dishonest seller can now safely discover the real winning bidders limit without having to double their transaction fee to obtain the information.
Cubicle has it right. Either you take on fraud by the horns, or it takes you on in very nasty ways. eBay and PayPal chose the latter course, and will always provide a high-cost, low reliability experience for the users. Luckily they got there in an environment when the competition wouldn't stay the course, but things have changed in the payments business lately. Signs are that they recognise the party's over, and Paypal are madly diversifying their base into credit cards and cell/mobile payments.
Viega and Messier talk in ACMQueue about how using SSL to get security is likely to be a bit of a fantasy:
Security Is Harder Than You Think, by John Viega and Matt MessierMany developers see buffer overflows as the biggest security threat to software and believe that there is a simple two-step process to secure software: switch from C or C++ to Java, then start using SSL (Secure Sockets Layer) to protect data communications. It turns out that this naïve tactic isn't sufficient. In this article, we explore why software security is harder than people expect, focusing on the example of SSL.
I'd agree - saying that you use TLS for your security model has generally correlated with a lightweight approach. Likewise, Bruce Schneier writes in Interactions of the ACM that two factor tokens are "too little, too late."
Man-in-the-Middle Attack. [phishing ... snipped]Trojan Attack. An attacker gets the Trojan installed on a user's computer. When the user logs into his bank's Web site, the attacker piggybacks on that session via the Trojan to make any fraudulent transaction he wants.
See how two-factor authentication doesn't solve anything? In the first case, the attacker can pass the ever-changing part of the password to the bank along with the never-changing part. And in the second case, the attacker is relying on the user to log in.
Although people are now happy to point out that the SSL, certificate infrastructure, and the browser security model out there is like swiss cheese, there still seems to be a sense that if the developers and the implementers just read the right books and just did the job fully, then we would have security ... I think the major point here is that ACMQueue and Interactions are happy to print articles pointing out the flaws which is probably a necessary step if we are to move forward.
March 31, 2006
Random Pennies
A curious remark from a German bank called Postbank about their desire to use digital signatures:
The electronic signature, which the bank attaches to its e-mail, is issued by TC Trust, the German subsidiary of GeoTrust.Only Postbank customers using e-mail applications with both S/MIME authentication and TC Trust certification will receive a certification symbol, confirming that the text message is from the bank, according to Ebert.
Currently, only Outlook supports the Postbank service, he said.
Confused. I think he means that TC Trust's root isn't in other mail clients. More curioser is this:
Plans are underway to switch the certification service from TC Trust to VeriSign, which already provides certification services for Postbank's Web pages, according to Ebert. "We started with TC Trust but we think it's better to have everything with Verisign, which is more widely used," he said.
While on the subject of phishing (Internet fraud maybe being the #1 topic in netnews over time) here's a list of myths in phishing:
Secure, encrypted web page indicates a valid website - Contrary to a popular advise, never rely solely on "https://" prefix or padlock icon that indicate a "secure" page. It is possible for a phishing website to have a valid SSL certificate.
Yeah, heard that one before :) There are 10 more. Meanwhile, the US DoJ conducts a large survey and finds:
About 3 percent of all households in the U.S., totaling an estimated 3.6 million families, were hit by some sort of ID theft during the first six months of 2004, according to DOJ data set to be released Sunday. ... According to the DOJ's numbers, credit card misuse is the most common consequence of identity theft. It accounted for about half of the cases of identity theft that the survey tracked, Baum said.Of the other identity theft victims, about 25 percent had banking and other types of accounts used without permission, 15 percent had their personal information misused, and about 12 percent faced a combination of several types of ID theft.
The average loss from these crimes amounted to US$1,290, with two-thirds of respondents saying that the theft cost them money. Based on these numbers, the nationwide estimated loss during the six months of the study amounted to $3.2 billion, for an annualized total of $6.4 billion.
Risks points at a costly burger mistake:
Four burgers at his neighborhood Burger King cost George Beane a whopping $4,334.33.Beane ordered two Whopper Jr.s and two Rodeo cheeseburgers when he pulled up to the drive-through window last Tuesday. The cashier, however, forgot that she'd entered the $4.33 charge on his debit card and punched in the numbers again without erasing the original ones - thus creating a four-figure bill.
...
Terri Woody, the restaurant manager, said Burger King officials tried to get the charge refunded. But the bank said the funds were on a three-day hold and could not be released, Pat Beane said.The hold is designed to prevent customers from spending money that no longer is available in their accounts and to let the bank confirm a transaction is legitimate before transferring funds, said Bank of America supervisor Joel Solorio.
Could have been worse ... could have happened on a stock exchange.
February 23, 2006
iVirus, Mr & Mrs Smythe, Shaking the Incumbents, Ping on convenience, Gmail on inconvenience
Curious that Apple's Safari wasn't mentioned in recent discussions about High Assurance certs. Which brings us to a rash of sightings of Mac Viruses. Well, three at least. Unfortunately the media can be relied upon to over-play the appearance of Mac Viruses, and downplay the Microsoft ones. That's because one is rare and the other is common. Although that will change over time, I predicted Macs won't be overly troubled by it this year, so they'd better do the right thing!
More signs of aggressive play by media corporates seen. This time, "Mr & Mrs Smith" have been accused of playing on your PC with more than the normal funny going's on. It's not clear what it means when they say "like a root-kit" but maybe you should play that movie at your mother-in-law's place first.
Dave discusses the effect of Skype on the telecoms industry. Curiously, although these forces have been building up for a decade (does anyone remember the first IP phone?) and we've been discussing it for even longer, it takes a big success like Skype to actually shake the incumbents. Exactly the same thing is happening in the DRM world as the incumbents are waking up to the success of iPod. Business plans and ideas are flashing around just like the good old dotcom days.
Ping launches an essay on how to solve phishing. He starts out from a principle that bears thought:
I have an idea about how to solve the phishing problem. Although proposals to solve phishing are not yet as common as proposals to solve spam, there certainly have been quite a few of them, so you would be right to wonder what makes this proposal any different or any more likely to work.So, right up front, here is the key property of this proposal: using it is more convenient than not using it.
This principle has been bubbling around for some time, awaiting a pithy encapsulation. Think about it - you use Skype because it is more convenient than not. You use SSH for the same reason. You probably benefit from SSL when you benefit only because you had to do nothing to make it happen. And Philipp points at how easy it is to turn off security:
Without any guarantees, here are two tips that will make sure you will receive these new features as soon as they are available (and if you're lucky, they will start working right away):If you are using an https connection to access GMail, remove the 's' (i.e. the address should read "http://mail.google.com"). Eventually, all the new services will support https, but they typically don't initially...
The comments are worth a read - for any security guy that needs to be reminded about how users really respond. Including this one which has more FC significance:
Embedding Google Talk inside Google Mail is going to create a real problem for some people.I work for a bank where all external IM is forbidden. We can only go through auditable internal IM applications. This is enforced by a proxy server that blocks access to all known IM servers including MSN Messenger, Yahoo, ICQ, AOL, Google Talk, Jabber, etc.
If the Compliance nazis hear that we can access Google Talk from Google Mail, they will block Google Mail too.
I don't suppose there's much hope in asking, but is there any way we can have a special version of Google Mail _without_ access to Google Talk?
Posted by: Anonymous Banker at February 10, 2006 03:17 AM
February 14, 2006
Birch on Blogs, decimal points matter with houses, too, and Bill Gates predicted...
News snippets for today: Dave Birch steps into the blogging world with Digital Money. Welcome! Dave is one of the grandfathers of FC, having led Consult Hyperion, spiritually at least, through a thousand and one conferences, work outs, contracts and so forth, all in their narrow field of technomoney and other things valuable.
Several people sent me references to this house that was erroneously valued at $400million. Now, such a blunder is just a typing mistake .. until the value gets fed into the budget, and the money gets spent before it is collected:
Most local officials did not learn about the mistake until Tuesday, when 18 government taxing units were asked to return a total of $3.1 million of tax money. The city of Valparaiso and the Valparaiso Community School Corp. were asked to return $2.7 million. As a result, the school system has a $200,000 budget shortfall, and the city loses $900,000.
Many people will look for many excuses in many strange corners ... but the answer is clear - don't spend money that doesn't exist. Corollary - use a real hard money system, not one based on promises. It won't happen again, I promise.
Dave points at bit-tech that checks the predictions of Bill Gates. Here's one:
What do you carry on your person now? Probably at least keys, identification, money, and a watch. Quite possibly you also carry credit cards, a checkbook, travellers checks, an address book, an appointment book, a notepad, reading material, a camera, a pocket tape recorder, a cellular phone, a pager, concert tickets, a map, a compass, a calculator, an electronic entry card, photographs, and perhaps a loud whistle to summon help.Youll be able to keep all these and more in another information appliance we call the Wallet PC. It will be about the same size as a wallet, which means youll be able to carry it in your pocket or purse. It will display messages and schedules and also let you read or send electronics mail and faxes, monitor weather and stock reports, and play both simple and sophisticated games. At a meeting you might take notes, check your appointments, browse information if youre bored, or choose from amongst thousands of easy-to-call-up photos of your kids.
Rather than holding paper currency, the new wallet will store unforgeable digital money...
Whether it happened like that or not, we'll leave others to judge. Or you can what Dave wrote.
February 06, 2006
The last (US) telegram, another FV copycat, another signature snafu
Western Union sent its last telegram last week. That's a communications method that then survived 150 years - a salutory reminder as to how long some networks take to die. Perhaps in 100 years or so we'll read about the last IPv4 packet...
Samuel Morse, inventor of the Morse Code, sent the first telegram from Washington to Baltimore on May 26, 1844, to his partner Alfred Vail to usher in the telegram era that displaced the Pony Express.It read, "What hath God wrought?"
No news on what other countries are doing, typically.
WSJ writes on Paypal's response to Googles "imminent" entry into the payment systems business.
But PayPal must now contend with Google. The Mountain View, Calif., Web-search giant, which has terrified Silicon Valley with its ability to quickly create new consumer products and services, is developing a rival service called GBuy. For the last nine months, Google has recruited online retailers to test GBuy, according to one person briefed on the service. GBuy will feature an icon posted alongside the paid-search ads of merchants, which Google hopes will tempt consumers to click on the ads, says this person. GBuy will also let consumers store their credit-card information on Google.Google said that it has acknowledged publicly on many occasions that it is working on payment products. The company also said it already processes online payments for ad services, as well as fees from consumers who use features such as Google Store and Google Earth. It declined to comment on any pending products.
Basically, Google is going the conventional copy-Paypal route. Install a credit card with Google, buy your retail products and get Google to aggregate the payments. You'll probably have a balance and be billed monthly. This is the same model that First Virtual pioneered, and muffed. Paypal refined it slightly (removed the two obvious bugs) and won big time. (Peppercoin tried this, not sure how they are doing.)
Why then is it taking so long? One wonders, but I'd speculate that for Google the honeymoon is over, and they have to dot the i's and cross the t's. If they muff it they might not get a second chance. Just speculation, mind.

In non-digital signature news, consider the plight of the Chairman of Qantas caught red-handed with copies of aircraft plans on entering american airspace:
Yet when the TSA rifled through her bag last year at Los Angeles Airport, their discovery of aircraft diagrams got them salivating. "Why have you got all this this?" one asked. "'I'm the chairman of an airline. I'm the chairman of Qantas," replied Margaret. "But you're a woman," replied the TSA goon. ... After a one hour interrogation and with TSA officials unimpressed by Margaret's production of official Quantas letterhead documents, she devised a way out that speaks volumes about the nature of this whole farce.She simply wrote a note to the TSA official saying that she was CEO of Quantas and signed it.
Notice two interesting issues other than the obvious that the TSA doesn't know what planet it is on. Firstly the checker was trained to pick up on inconsistencies and picked up that a woman was calling herself Chairman. In California, that's inconsistent and politically incorrect. In Australia, that's more like a statement of pride. Oops. So there is an obvious limitation in teaching sophisticated checking of cultural cues to someone who has never left California.
Secondly, a signed statement carries enough weight to have over-ridden the entire process. What does that say about signatures? What does that say about bureaucracies and social engineering? Can you imagine the Chairman whipping out her smart card, inserting it into the TSA's reader and digitally signing a statement?
(Which brings to mind the infamous digital signing story from the 90s when the US President and the Irish PM used smart cards to sign an ecommerce agreement... After signing the treaty, they swapped the smart cards as if they were football jerseys...)
February 01, 2006
Startups, Free Banking, Gift cards
Pelle points at Guy who writes on The Art of Bootstrapping. For those who've done lots of startups the pain will be quite familiar. And for those who appreciated GP, Guy's #3 might resonate:
3. Ship, then test. I can feel the comments coming in already: How can you recommend shipping stuff that isn't perfect? Blah blah blah. Perfect is the enemy of good enough. When your product or service is good enough, get it out because cash flows when you start shipping. Besides perfection doesn't necessarily come with time--more unwanted features do. By shipping, you'll also learn what your customers truly want you to fix. It's definitely a tradeoff: your reputation versus cash flow, so you can't ship pure crap. But you can't wait for perfection either. (Nota bene: life science companies, please ignore this recommendation.)
Nick points to Lawrence White - of Scottish free banking fame - who notes that the free banking influence is being kept in the Federal Reserve Board by the nomination of Randy Kroszner, a noted austrian scholar.
Brief reminder: Retiring Chairman Greenspan, also known as Sir Alan in the anglo world, is the greatest friend that free banking and gold ever had. It was under his influence that the Federal Reserve declined to regulate gold as money, and thus left the scene open for the development of the DGCs. That holiday is now over.
On the question of new / old money forms other than gold, there is an increasing use of gift exchange in the US. A survey by Accenture found that:
More than four out of five survey respondents (82 percent) said they gave or received gift cards this holiday season, and two-thirds (66 percent) said they both gave and received them. The vast majority (81 percent) of respondents said they have already used their gift cards, almost half (43 percent) said they planned to spend their gift cards within one month of receiving them, and nearly two-thirds (63 percent) said they planned to spend the entire value of their gift cards in a single store visit. ... The growing popularity of gift cards has introduced a secondary market in which consumers can buy and sell the cards at a discount. Just 13 percent of survey respondents, however, were aware of the opportunity to purchase pre-owned, discounted gift cards. Even fewer respondents (9 percent) were aware of the opportunity to sell gift cards for cash.
82% ! Yowsa! That's almost as popular as vegemite. No news yet on what discount the sold-on cards move for. Nor on use of phone cards as money.
January 01, 2006
Rights in the New Year
Pennies for the New Year: An effort to document the ontology of the Rights layer:
Anonymity, Unlinkability, Unobservability,Pseudonymity, and Identity Management - A Consolidated Proposal for Terminology (Version v0.24 Nov. 21, 2005)
Also, IFCA have published their list of accepted papers for FC06 in Anguilla this February. Unfortunately, there are no abstracts posted that I saw, so titles only for the browsing.
From the real estate / property market, someone has taken on the brave step of offering individual issuance capabilities to house owners.
Todd points at an interesting paper on accounting for p2p systems with the goal of distributed accounting:
PeerMint: Decentralized and Secure Accounting for Peer-to-Peer ApplicationsAbstract. P2P-based applications like file-sharing or distributed storage benefit from the scalability and performance of completely decentralized P2P infrastructures. However, existing P2P infrastructures like Chord or Pastry are vulnerable against selfish and malicious behavior and provide currently little support for commercial applications. There is a need for reliable mechanisms that enable the commercial use of P2P technology, while maintaining favorable scalability properties. PeerMint is a completely decentralized and secure accounting scheme which facilitates market-based management of P2P applications. The scheme applies a structured P2P overlay network to keep accounting information in an efficient and reliable way. Session mediation peers are used to minimize the impact of collusion among peers. A prototype has been implemented as part of a modular Accounting and Charging system to show PeerMints practical applicability. Experiments were performed to provide evidence of the schemes scalability and reliability.
December 25, 2005
Merry Xmas all
Ah, have a nice Xmas!
Check in with F-secure for the original, and with EC for the significance.
November 04, 2005
Phishing for News..
George reports that his story originally published here in FC has made it to USAToday:
He watched, horrified, as the intruder in quick succession dumped $60,000 worth of shares in Disney, American Express, Starbucks and 11 other blue-chip stocks, then directed a deposit into the online account of a stranger in Austin. "My entire portfolio was being sold out right before my eyes," recalls Rodriguez, 41, a commercial real estate broker who alerted Ameritrade in time to stop the trades.
Also BusinessWeek but I was not able to find a URL. George's story is a great one if you are unsure how far phishing reaches! (Addendum: SEC releases advisory to traders.)
Some interesting sniping from the banks on two-factor tokens. The current generation of two-factor tokens (like RSA Security's SecureId) are the stocking fillers of the security field. Cute, cheap in small numbers and broken by January. This is a well written piece rounding up the issues:
But tokens create their own headaches. They're relatively costly to deploy and can prompt lots of calls to customer service if they're lost or temporarily out of reach. Banks also fear a "necklace" scenario in which customers end up collecting an annoying strand of tokens from all the companies they do business with online.Even one token might be seen as a hassle.
After ETrade Financial Corp. began offering tokens from RSA Security Inc. to its 2.8 million U.S. customers, only 20,000 signed up. Almost all those people could get the gadgets for free because they were frequent traders or had more than $50,000 in their accounts; everyone else had to pay $25.
That about matches the 1% takeup rate that I heard of in the gold sector, when someone tried to sell these things.
One-time passwords can be given out in less expensive ways. They can be beamed to a cell phone or handheld computer, or mailed to customers on scratch-off cards.But security experts warn that one-time passwords can be stolen in a "man-in-the-middle" attack, in which a con artist harvests a victim's code on a phony Web site and instantly relays it to the real bank, then conducts transactions in her name. Such frauds are rare -- if they happen at all -- but that's partly because there are so many easier targets, for now.
Token vendors point out that their devices can be set to foil men in the middle by generating additional codes for each individual transaction. Still, there are enough knocks against hardware-based solutions that most banks will take softer steps to meet the regulators' demands.
Not bad! Someone has done their homework. This is not to say that it can't be done better, and the Wikid token may be just that. I haven't examined it in detail but it essentially duplicates what the software tools to address phishing do - it caches the cert in some way. (Also see blog.)
October 14, 2005
Roundup on News
In the developing story of the "Cuthbert case" the ripples continue to spread as security experts disect the result. Curiously, it hasn't hit the mainstream much, probably because popular press can't work out what the fuss is about but the blogs seem to have it. Adam points at Samizdata.net Diana Quaver, who has followed and documented the case in much more detail. Also dropsafe has a nice roundup. Here's one article from ZDNet:
"Nobody thought he was doing anything significant or malicious, and there was a strong argument that the police should have given him a slap on the wrists and not prosecuted," said Sommer, senior research fellow at the London School of Economics' Information Systems Integrity Group.
Sort of. More usefully, what we are not confident about is that we can describe in terms that users will understand and that matches the web's ethos just what is "unauthorised" and what is not. We've now got a good theory as to what BT thought was unauthorised - but it isn't a theory that makes any sense to the user or the web, nor is it a theory promulgated much further than the minds of corporate security experts.
In terms of a trespassing analogue, there is no sign, no fence, and BT prosecuted the trespasser on the basis of finding his wallet dropped inside the facility. As the owner admitted to being inside, this was considered good enough for a criminal conviction - but it isn't good enough for trespassing!
This is a complete mess. I'd suggest not going anywhere near the DEC / BT.donate.com site to donate; or indeed anywhere near BT until they explain in terms understandable to users just what the difference between their website and the RFC is.
Read on for more news!
It's official: we now have a duopoly in CPUs as AMD has reached 50% of one particular market. This was a classic story that I picked when I realised that Intel had broken the golden rule that had established its hegemony - and started on the fatal journey to design another chip that wasn't Intel-compatible. AMD saw it too and went the other route of Intel-compatible-and-64 bits and won. By the time Intel had realised their mistake it was too late, and thanks to their mistake we all win with cheaper chips and more aggressive progress. Now if only Steve Ballmer would get distracted on ... dunno, how about DRM?
Interesting post about side-channel attacks on games software, a timing difference gave a player a way to clean up. Also, a curious finding for ISPs - DDOS is the #1 hassle:
Over 90 percent of ISPs surveyed cited simple "brute force" TCP SYN and UDP datagram DDoS floods from zombie PC networks as their biggest day-to-day hassle, a finding which should apply equally to their corporate clients. This puts DDoS ahead of more recent attack types such as fast-spreading worms and DNS poisoning, which were ranked second and third respectively, in terms of prevalence. Even then, worm attacks were often most hazardous in terms of their original effect on traffic. "The primary threat from worms is not the payloads but the network congestion they cause," the report noted.Surprisingly, given the prevalence of this type of attack in recent years, only 29 percent of ISPs offered services to counter and trace DDoS in an automated way at the ISP level. The majority only discovered such events when a customer contacted them for help. The main means of defending against DDoS remains the use of Access Control Lists (ACLs), but these come with the downside of shutting off network access. The DDoS attack is stopped but only by replicating much the same effect as the original traffic blocking.
The reported motivations for DDoS attacks clusters around issues such as cyber-extortion, electronic protests against companies, and even corporate espionage. Few, if any, of such attacks are reported to result in criminal action against the instigator, which could account for its continued popularity.
Nice the way they characterise it as a "hassle" and ignore the actual damage done to the target, which is presumably under some extortion play.
A very nice piece of Open Governance; eBay shareholders go through the annual report and talk about the stated risks there. Some good stuff on Paypal woes for payment systems people.
And finally a welcome sounding of the alarm: CIOs and vendors are complicit.
Those who've read my draft on silver bullets will know what this is about, but it is good to see someone else looking at the problem. Here's what Ed Lazowska (who holds the Bill & Melinda Gates Chair in Computer Science & Engineering at the University of Washington !!!) says:
Q: Some of the problems, such as software not being designed with security in mind, indicate that CIOs are somehow complicit. In your opinion, are CIOs victims or are they part of the problem?A: The answer surely is both. CIOs are partially responsible for the insecure state of today's operating systems, because they failed to see the handwriting on the wall and prioritize security. Vendors produce what we are willing to purchase. CIOs are largely responsible for the failure of their organizations to operate at the current state of the art with respect to cybersecurity, and very few organizations operate at the current state of the art.
Now, the problem is that you can't suddenly decide that you want something like security and expect to be able to buy it, because the technology doesn't necessarily exist. Almost no IT company looks ahead more than one or two product cycles. And historically in IT, those ideas comes from research programs that the federal government underwrites. Just think about e-commerce: You need the Internet, Web browsers, encryption for secure credit card transactions and a high-performance database for back-end systems. The ideas that underlie all of these can trace their roots to federally funded R&D programs.
That's how this relates to the R&D agenda. Long-range R&D has always been the role of the national government. And the trend, despite repeated denials from the White House to the Department of Defense, has decreased funding for R&D. And of the R&D that does get funded, more and more of it is on the development side as opposed to longer-range research, which is where the big payoffs are in the long term. That's a more fundamental problem that CIOs aren't responsible for.
I do not agree with the second part of his answer, but left it in for contrast!
September 10, 2005
Open Source Insurance, Dumb Things, Shuttle Reliability
(Perilocity reports that) LLoyds and OSRM to issue open source insurance, including being attacked by commercial vendors over IP claims.
(Adam -> Bruce -> ) an article of the "Six Dumbest Ideas in Computer Security" by Marcus Ranum. I'm not sure who Marcus is but his name keeps cropping up - and his list is pretty good:
- Default Permit (open by default)
- Enumerating Badness (cover all those we know about)
- Penetrate and Patch
- Hacking is Cool
- Educating Users
- Action is Better Than Inaction
I even agree with them, although I have my qualms about these two "minor dumbs:"
- "Let's go production with it now and we can secure it later" - no, you won't. A better question to ask yourself is "If we don't have time to do it correctly now, will we have time to do it over once it's broken?" Sometimes, building a system that is in constant need of repair means you will spend years investing in turd polish because you were unwilling to spend days getting the job done right in the first place.
The reason this doesn't work is basic economics. You can't generate revenues until the business model is proven and working, and you can't secure things properly until you've got a) the revenues to do so and b) the proven business model to protect! The security field is littered with business models that secured properly and firstly, but very few of them were successful, and often that was sufficient reason for their failure.
Which is not to dispute the basic logic that most production systems defer security until later and later never comes ... but there is an economic incentives situation working here that more or less explains why - only valuable things are secured, and a system that is not in production is not valuable.
- "We can't stop the occasional problem" - yes, you can. Would you travel on commercial airliners if you thought that the aviation industry took this approach with your life? I didn't think so.
There's several errors here, starting with a badly formed premise leading to can/can't arguments. Secondly, we aren't in general risking our life, just our computer (and identity as of late...). Thirdly, it's a risk based thing - there is no Axiomatic Right From On High that you have to have secure computing, nor be able to drive safely to work, nor fly.
Indeed no less than Richard Feynman is quoted (to support #3) which talks about how to deal and misdeal with the occasional problem.
Richard Fenyman's [sic] "Personal Observations on the Reliability of the Space Shuttle" used to be required reading for the software engineers that I hired. It contains some profound thoughts on expectation of reliability and how it is achieved in complex systems. In a nutshell its meaning to programmers is: "Unless your system was supposed to be hackable then it shouldn't be hackable."
Feynman found that the engineering approach to Shuttle problems was (often or sometimes) to rewire the procedures. Instead of fixing them, the engineers would move the problems into the safety zone created conveniently by design tolerances; Insert here the normal management pressures including the temptation to call the reliability as 1 in 100,000 where 1 in 100 is more likely! (And even that seems too low to me.)
Predictibly Feynman suggests not doing that, and finishes with this quote:
"For a successful technology, reality must take precedence over public relations, for nature cannot be fooled."
A true engineer :-)
See earlier writings on failure in complex systems and also compare Feynman's comments on the software and hardware reliability with this article and earlier comments.
August 12, 2005
WoT in Pictures, p2p lending, mailtapping
Rick points at a nice page showing lots of OpenPGP web of trust metrics.
The web of trust in OpenPGP is an informal idea based on signing each other's keys. As it was never really specified what this means, there are two schools of thought, being the one where "I'll sign anyone's key if they give me the fingerprint" and the other more European inspired one that Rick lists as "it normally involves reviewing a proof of their identity." Obviously these two are totally in conflict. Yet, the web of trust seems not to care too much, perhaps because nobody would really rely on the web of trust only to do anything serious.
So an open question is due - how many out there believe in the model of "proving identity then signing" and how many out there subscribe to the more informal "show me your fingerprint and I'll trust your nym?"
What's this got to do with Financial Cryptography? PKI, the white elephant of the Internet security, is getting a shot in the arm from web of trust. In order to protect web browsing, CACert is issuing certificates for you, based on your subscription and your entry into a web of trust. In one sense they have outsourced (strong) identity checking to subscribers, in another they've said that this is a much better way to get certificates to users, which is where security begins, not ends.
More pennies: I've got my Thunderbird and Firefox back, so now I can see the RSS feeds. I came across this from Risks: How to build software for use in a den of thieves. We'd call that Governance and insider threats in the FC world - some nice tips there though.
PaymentNews reports that PayPal CEO Jeff Jordan presented to Etail 2005:
Nearly 10 percent of all U.S. e-commerce is funneled through PayPal, according to Jordan. One out of seven transactions crosses national boundaries. Consumers in more than 40 countries send PayPal, and those in more than 20 countries receive this currency."Our goal," he said, "is to be the global standard for online payments."
(More on Paypal.) And more from Scott:
Eliminate the banking middle man -- that's what Zopa's about. Rebecca Jarvis reports for Business 2.0 on what the UK's Richard Duvall is up to with Zopa.Are you a better lender than a bank is? Richard Duvall, who helped launch Britain's largest online bank, Egg, thinks you are. His new venture, Zopa, is an eBay-like website that lets ordinary citizens borrow money from other regular Joes -- no bank needed.
In mailtapping news from Lynn, a US court of appeals reversed a ruling, and said that ISPs could not copy and read emails. Meanwhile a survey found that small firms were failing to copy and escrow emails as instructed. And we now have the joy of companies competing to datamine the outgoing packets in order to spy on insider's net habits. The sales line? "every demo results in a sacked employee..."
E-mail wiretap case can proceed, court says
Study Finds Small Securities Firms Still Fail To Comply With SEC E-mail Archiving Regulations
When E-Mail Isn't Monitored
In closing, Everquest II faced off with hackers who had found a bug to create currency. We've seen this activity in the DGC world, and it no doubt has hit the Paypal world from time to time; it's what makes payment systems serious.
July 30, 2005
Disclosure, Victims, and Browsers reveal anti-phishing approaches
A couple of articles on disclosure - one about the Cisco hole which was revealed at Blackhat, and another from Oracle's CSO who trots out some mild reasons why security reasons shouldn't cause trouble.
Security researchers generally work for free when they do public disclosure, and they represent the thousands or millions of users who cannot get help at any cost. As companies like Cisco and Oracle charge through the nose but don't offer any compensation for their victims, I think their case is weak. Some costings on burnt credit card numbers:
Canceling an account and reissuing cards is a costly proposition for card issuers. The process costs Discover $39 per account, according to Kniola. That’s why Discover prefers to monitor potentially compromised accounts if no suspicious activity has occurred rather than do blanket re-issues.
Both the bank and the credit card holder here are victims. More news from those who aren't victims. Microsoft, AOL and Mozilla recently revealed their anti-phishing strategies.
WholeSecurity, which is privately held, is helping Microsoft assemble and maintain a list of verified phishing sites, also known as a blacklist. When people try to visit a Web site on the list, IE7 automatically warns them via a dialog box that the site is fraudulent and suggests they "not continue to this Web site." At that point, people can close the Web page, or continue on if they choose.
WholeSecurity, via a project called the Phish Report Network, has thousands of Web sites in its blacklist and adds more all the time from the hundreds of new sites that contributors flag daily, said John Ball, senior product manager at WholeSecurity. Microsoft helped the company launch the Phish Report Network in February, along with Visa, eBay and eBay's PayPal unit, which all help to build and maintain the list.America Online's Netscape unit introduced a new version of the Netscape browser in May with a similar feature. The company has compiled its own blacklist with the input of parent AOL, nonprofit privacy group Truste, VeriSign and security software company Paretologic.
Following on from Netcraft, that's 2 more votes for blacklisting. Oddly, after a year of humming and hahing:
The Mozilla Foundation has decided not to incorporate antiphishing technology into its increasingly popular Firefox browser, opting instead to focus on the e-mail side of the problem. An upcoming version of Mozilla's Thunderbird e-mail program is designed to alert users to messages containing links to phishing sites, said Chris Hofmann, director of engineering at the Mozilla Foundation.
Go figure. The problem with stopping it at the mailer is that the mailer hasn't proven that successful at dealing with ordinary spam (Tbird gets about 50% in my experience), it doesn't do anything for the bulk of Firefox users (those who do not use Thunderbird) and not all phishing comes from email.
The Thunderbird program will rely on a tool that automatically analyzes the attributes of links, rather than on a blacklist, Hofmann added. "The large volume of content, and the dynamic nature of the Web, make managing a list of potential phishing sites an incredibly hard job," he said.
Right, I'd agree with that. But Hofmann is only revealing half the story. Better technologies were on offer to Mozilla - TrustBar, Petnames and even stuff Mozilla had developed internally are winning converts as browser toolbars.
As reported we are now in an arms race. Only speed will help now:
For instance, more phishers are registering domain names for their sites rather than using numeric Web addresses, he said. Lin believes it's a response to the fact that Deepnet's browser has been warning people that sites lacking domain names are suspicious."The phishers will find some other way," Lin said. "It's like antispam. There are antispam programs, and spam still exists. We have anti-spyware, and spyware still exists."
Yup. For a solution that would take a year to conceive and roll out, it would probably take a month for a good phishing outfit to attack. Get used to it.
July 07, 2005
Fear-commerce, something called Virtualisation, and Identity Doublethink.
According to pipeline, "E-commerce is buried beneath a blanket of fear. Online purchases, according to some observers, are down by nearly half; Internet banking by nearly a third." I'm not sure I believe that bad, but has anyone heard any stats? Seen any drop-off? This second CNN article disagrees, but a survey from Pew (Register reports) says that 90% of americans have done at least one thing to deal with the current threatening online environment:
The survey found:
* 81 per cent of net users say they have stopped opening unsolicited email attachments Half those quizzed (48 per cent) say they have stopped visiting potentially dodgy web sites out of spyware concerns
* A quarter (25 per cent) of those questioned said they have stopped downloading music or video files from peer-to-peer networks in order to avoid getting unwanted software programs on their computers.
* A minority of surfers (18 per cent) say they have changed the web browser software they use in order to avoid malware attack
The same survey also found suggestion that people are ignoring the security advice of suppliers such as Microsoft, which makes perfect sense to me, as their advice on security has to be politely termed as 'conflicted'. Lynn Wheeler reports on on their claim that they are doing "virtualisation" and security has to wait until that is done. Seeing as I don't understand those words, I can't comment on how plausible this excuse is!
Microsoft confirms plans for virtualization hypervisor - Computer Business Review
(Anne & Lynn Wheeler, Wed Jun 29 16:03:10 2005)
i'm at annual ieee chip conference ... it is invitation only so they can talk about non-public information. late yesterday the senior engineer from amd, gave a talk on futures. he was introduced as having spent some amount of his career starting in '62 building cryptographic hardware at nsa and having been one of the primary co-authors of the orange book. he didn't mention security in his talk ... but in the Q&A afterwards somebody asked about security. He commented that you probably aren't going to really see it until virtualization.Turns out this is what i did during the 60s and 70s ... and i got con'ed into be chair of next year sessions on "security, authentication, partitioning, and virtualization". slightly indirect reference.
Also from Lynn, for those interested in the background behind the CardSystems breach, here's a good article. Yes, it really does say that Cable and Wireless are their security auditor...
And over in Australia, it seems that the notion that centralised identity means easy identity theft is starting to gain traction:
But Mr Ruddock told a security technology conference in Sydney today a national ID card could actually compromise Australians' security."We haven't supported an approach where all personal information is centralised on one database and a single form of identification is used," Mr Ruddock told the gathering of government, security and business leaders.
Such an approach could actually increase the risk of identity fraud because only one document would need to be counterfeited to establish an identity.
It is significant that people are starting to think about the problem. Consider the British view:
When the experts were asked whether the government's all-singing and dancing electronic ID card would solve the problem, there was hollow laughter all around. It would simply locate all identities in one place, creating an El Dorado for phishers.
The hollow laughter reflects the British Government's current claim that an identity card will stop terrorism, benefit fraud, and make a nice hot cup of tea, all for the bargain price of 100 of their quaint old sterling pounds.
A rather sterling performance by the London emergency services in this morning's tube and bus bombings focusses attention on the terrorist threat. Dare we ask: would the bombers would have had to show their identity to get on the bus? I don't think so, and I'm personally very impressed with the concentration by the Brits on the real issues: setting up crime scenes, getting the areas cleared and people back to work, and refusing to play the media's game of spreading panic and mayhem.
Finally, Tao describes how banks in america are now employing computers to phone you up to ask you about your credit card transactions. I wonder if such computers are too expensive for phishers, or whether they are well enough funded to overcome that barrier already?
June 27, 2005
Definitions, competition-by-regulation, and Justice-by-Press-Release
I had a go at upgrading the Wikipedia definition of Financial Cryptography. Anyone can edit it and improve on it, and I left you plenty of room for that!
I also added an article on Token Money as I saw it. Curiously, it may be a definition that only exists in the FC world! The Money entry in Wikipedia saw it differently, referring to tokens as those that had no intrinsic value (by which it meant gold). Any economists in the house to rule on this?
SL points me to Simpay, a pan-european mobile phone payments system that has decided not to roll out everything ... in what appears to be a response to the overbearing regulation by the EU. Donald at linkdump has a few choice words on how the regulators now get to clean up the mess they made:
Mobile operators make money by exploiting their own quick-and-dirty payment mechanisms and (inter)national roaming agreements for the interoperable use of these instruments. With Simpay they found out what it would cost to build and operate a system that really accounts for all transactions. Also, they may have started to discuss interchange fees for Simpay, the applicable Regulation 2560 as well as the future legal framework for payments in the European Market.The conclusion could then well have been that they are far better of with the current grey-area, less-visible payment arrangements than with a formal payment processor that has no business case to work on. The benefit: more income from payments business while maintaining less visibility and transparance.
Well, of course. The regulations were put in place to protect the banks from competition, and the competitors' mission is to avoid the regulations. Society cheers you on! Speaking of regulating banks, what have you to say about the chart 1/3 way down in this article:
The Economist (thanks, Ron!) weighs in on the data crisis in the USA. Not much to say other than they've picked up a series of soundbites from b-school profs who all think the board should pay more attention. With opinions like that it's no wonder the data gets lost. But it gets worse:
The FTC decided to settle with BJ's Wholesale Club, a retailer whose lax data-protection practices the agency said constituted an “unfair practice that violated federal law.” The firm collected too much data, kept it too long, did not encrypt it, lacked password protections and left its wireless network open. This, in turn, enabled criminals to produce counterfeit credit and debit cards using stolen customer data and rack up millions of dollars in fraudulent charges. The firm has agreed to fix these problems and undergo information-security audits for 20 years.
So the FTC is getting tough, but what's with the "information-security audits for 20 years" nonsense? Straight on to KPMG, then. Confirming the judicial flavour of issuing justice only at arbitrary times and places, the discussion surrounding the pending and alleged KPMG indictment is centering around whether we really need to stick another barb in the already wounded animal known today as the Big Four Accounting Firms:
Some accounting experts said that, while an indictment could surely ground KPMG, it would not bode well for the accounting industry. Dozens of top notch corporations had to scramble around the world to find a new auditor after Arthur Andersen was brought down by an indictment over its role in the accounting fraud committed at energy trader Enron Corp.There does not seem to be any appetite for reducing the number of audit firms any more. It is already difficult enough for a large corporate entity to retain the size and sophistication of auditors. (An indictment) will be intolerable," said Mark Cheffers, head of auditor research firm Audit Analytics.
What ever happened to compassion and the right to a speedy trial? If the audit is dying, put it out of its misery! The public has little faith in audits, so what's the point?
And over in gambling territory, the poker players are calling the US Department of Justice's bluff. The now legendary 5 billion pounds IPO of just one of the online poker companies has drawn out the DoJ in a its approach to gambling - tell everyone that gambling is illegal, but don't actually litigate so aggressively just in case they are wrong.
One has to applaud the poker players in this. If justice is to be done by press release not law, then what happens when various officials decide to misinterpret the law for their own purposes?
I saw a perfect of example of regulation by press release becoming a protection subsidy over at the Wikipedia definition of money where some innocent said that Western economies ban the private issuance of money. That's not actually the case, and it is explicitly not the case to my knowledge in USA, Europe (the eMoney directive), New Zealand, Australia and one supposes any country that has ever trialled a smart card money. Luckily, it looks like someone else saw it and corrected the flaky text in a couple of days. Pretty snappy those Wikipedia folks!
Tao reports (here and here) on the CISSP certification, a common test you can take to become a security professional. So my question is: is a CISSP a neutral signal? And if not is it negative or positive? And what do I do with this CISSP spam I'm now getting?
June 17, 2005
Hype is free, Common Sense costs Pennies
Phishing news: puddle phishing (targetting small banks) is on the rise, as is phishing outside the US. Both of these are to be expected as phishers move around and try new things. One might suspect that the major US financial institutions have been 'phished out' but I wouldn't say that yet. The browser infrastructure remains riddled with too much swiss cheese security for any but a politician's declaration of victory, and it will be interesting to see how successful DNS attacks are at raising more funds from the hapless victims.
Amid yesterdays's flood of identity/phishing news, there are reports that identity theft is bigger in the US than anywhere else. Long reported in these pages as primarily a US problem, it turns out that people inside the US have now noticed this: Lower Overseas Rates Of Identity Theft Could Guide U.S. Lawmakers, and Privacy Advocates: Look Overseas For Lower Identity Theft Rates (both the same content).
And if you think your data is being phished by crooks, think again. The US Department of Justice is seeking to make matters worse by mandating data collection by the ISPs. Perry quotes this Article:
The U.S. Department of Justice is quietly shopping around the explosive idea of requiring Internet service providers to retain records of their customers' online activities.
More data collected, more value. More value, more theft. We saw the same kneejerk reaction a few months back when Elliot Spitzer floated the idea of making an extra crime. Truly dumb, truly guaranteed to reduce security.
In crypto news, the how to crack SHA1, SHA0 papers from the Shandong team are now released on Prof Wang's site. Good work, but attention is now switched to Dan Boneh's timing attack on AES (also 1 and 2). Slightly embarrassing for the NIST assessment that didn't pick it up, but no need to panic - make sure your AES is constant time.
In closing, some rare common sense spotted in security reporting. Gartner, long a packager of other people's nonsense, has issued its list of 5 most hyped security issues. And, they actually aren't that far off the mark:
- IP (Internet Protocol) telephony...
- malware for mobile devices...
- Fast-moving worms that infect the entire Internet within minutes...
- Wireless hot spots...
- Sarbanes-Oxley financial reporting rules...
It's about time someone stood up and pointed out who's selling clothes to the Emporer (someone like Tao?).
Are Security Threats Really Overhyped?Some experts say VoIP security and mobile viruses already are serious problems.
Grant Gross, IDG News Service Monday, June 13, 2005
Two Gartner analysts released their list of the five most overhyped IT security threats, with IP (Internet Protocol) telephony and malware for mobile devices making the list, but not all IT security vendors agree with the analysts' assessment.
Lawrence Orans, principal analyst at Gartner, and John Pescatore, vice president and Gartner fellow, noted that while attacks on IP telephony and mobile devices may come eventually, current warnings about security problems are ahead of actual attacks.
"Securing IP telephony is very similar to securing a data-only network," Orans said during a presentation last week at the Gartner IT Security Summit in Washington, D.C. "The fact that you could capture packets with e-mail isn't being covered in the trade publications."
Recent concerns about eavesdropping on IP telephony calls have discounted the fact that it's nearly impossible to eavesdrop without being inside of the building where an IP call is initiated or received, with eavesdroppers needing access to the corporate LAN, he said. "It's not really happening on any networks today," he said.
Different Opinion
Not everyone agreed with Gartner's assessment, however. Companies deploying IP telephony or voice over IP services do need to pay attention to security, and users of IP telephony need to protect not only the end-device phones and IP servers, but also signaling and other voice equipment, said Stan Quintana, vice president of managed security services for AT&T. "It's a slightly different, more complex equation than data networks," he said.
The two Gartner analysts see large businesses delaying IT improvements such as wireless LANs because of "overhype" over security threats, they said.
Too much hype on some threats may distract businesses from focusing on other, real threats, added Tom Grubb, vice president of marketing for Vormetric, a data security vendor. This year, a series of massive data breaches at several large companies have occurred, and protecting against data theft, and protecting against insider threats, may be more important than worrying about issues such as malware for mobile devices, he said.
"I think their point was, these things may be threats, but you have to keep your eye on the ball," added Grubb, who attended the Gartner summit.
ID theft and spyware are threats that have gotten a lot of attention lately because they are real, prevalent risks, added Richard Stiennon, vice president of threat research for Webroot Software, an antispyware software vendor.
Going Mobile
Some security vendors have focused on malware for so-called smart phones and other mobile devices, but such devices run on a number of operating systems, unlike the Windows dominance on desktop and laptop computers, Pescatore said. Without a dominant mobile operating system for at least a couple of years, mobile viruses or worms will have a limited impact, he said.
"For any piece of software, somebody can write an attack," Pescatore added. "The key issue is: can somebody write [a mobile attack] that will spread quickly and rapidly and cause more damage to your enterprise than it will cost you to prevent that damage?"
Some security software vendors have hyped mobile malware as a potential problem as a way to expand their business beyond the traditional desktop and laptop markets, Pescatore said. Only about 3 percent of consumers and workers have smart phones and PDAs with always-on wireless connections right now, he added.
"You can see the glint in the antivirus vendors' eyes when they think of the billion mobile phones out there," added Webroot's Stiennon.
A representative of antivirus vendor Symantec said the company isn't trying to hype mobile device threats, but trying to educate users as mobile devices become capable of storing more information. While mobile device security isn't a big issue now, that could change in coming years, said Vincent Weafer, senior director of Symantec Security Response.
"The risk changes dramatically in a short amount of time," Weafer said. "What we're trying to tell people is, if they're deploying these devices, they should deploy them in the right way."
Vormetric's Grubb agreed that mobile malware shouldn't be a top-priority concern for most large businesses, but mobile device security is becoming an issue. As more workers use more powerful mobile devices, companies need to be concerned with the physical security of mobile devices and about what mobile devices are downloading from their networks, he said.
Companies need to be concerned about what kinds of malware mobile devices can bring into a corporate network, added AT&T's Quintana. "The convergence of our networks is a double-edged sword," he said. "It's providing a high level of risk. It's not overhyped."
Also On the List
* Also on the list of overhyped security threats, according to Orans and Pescatore:
Fast-moving worms that infect the entire Internet within minutes will make the Web unreliable for business traffic and virtual private networks (VPNs) . While the SQL Slammer worm in 2003 did much of its damage within 15 minutes, that's the only such example so far of a so-called Warhol worm, Orans said. The analysts predicted that the public Internet will continue to remain a low-cost, safe alternative to closed data networks, although they recommended companies consider using VPNs.* Wireless hot spots are unsafe. While uneducated wireless users can fall victim to hackers, corporations have tools such as VPNs to protect wireless data, Pescatore said. Some wireless carriers and wireless security vendors also offer tools that validate an access point's identity and reduces the risk of connecting to a hacker's access point. Targeted attacks on corporate networks, not picking off wireless user data, is where the money is, said Reed Taussig, chief executive officer of Vormetric. "That's a much larger return on investment than sitting around Starbucks waiting for someone to enter a credit card at Amazon.com," Taussig added. "Hanging around at Starbucks waiting for someone to make a mistake is the definition of a stupid criminal."
* Finally, the Gartner analysts suggested that some vendors are hyping regulatory compliance as a way to achieve security. Regulations such as the U.S. Sarbanes-Oxley financial reporting rules are focused primarily on other issues besides IT, but many corporations remained concerned about compliance reporting, Pescatore said.
"[The hype] often distracts that spending into compliance reporting rather than increasing security," he said.
Steve Roop, vice president of marketing for data loss prevention vendor Vontu agreed. "There's a large number of solutions providers who claim that what they do is the silver bullet," he said.
Pinch me, I must be dreaming!
June 13, 2005
Killing for Pennies, and is AOL, the "gateway drug", cause or cure?
News in virtual gaming property continues to madly echo real life, as a man in China was sentenced for killing a friend after the latter sold his sword for a knight's ransom - 7,200 Yuan (£473). As readers will know, this follows on news of a single island being sold for a fortune and the outrage of cyberspace imitating life (fraud, murder, rape, verbal abuse, hit & run driving discussed in To Kill an Avatar).
A paper at Economics & Security conference on stock market effects from vulnerability announcements got some press.
(to follow: "security isn't working" and the LexisNexus hack...)
When I read that they'd measured a 0.2% drop in Microsoft shares after a vulnerability announcement, I immediately thought this was suspicious. How can the market respond to known news so stupidly? Commentary here is more incisive and critical, pointed to by Adam. Bad news effecting stock prices is a well studied phenomena; there are some other studies on vulnerability and hack announcements.
Rumour of "security isn't working" continues to circulate. Here's a post by Marcus Ranum that tries to draw some conclusions on why security expenditure is sky-rocketing and security is getting worse. Pointed to by Tao. Of course, the conclusions will be easy to disagree with - Marcus assumes binary security values not risk values - but the logic he uses to get to his conclusions is good.
And more on security - if you ever wanted to understand hackers as your threat, have a read of the Wired article on the LexisNexis hack (this is the one where a cop's laptop was breached and this led to getting access to celebrity files and so forth...).
For those who already know what hacking is about, I'll leave you with these choice snippets which address lousy security. The big question - what do we do about lousy security? Is it a fact of life or something we must eradicate? Cause or cure?
Database Hackers Reveal Tactics By Kim Zetter...
Hacking began with AOL
Cam0 is also a suspect in the recent security breach of socialite Paris Hilton's T-Mobile account and was investigated last summer after admitting to Wired News that he hacked America Online and stole AOL Instant Messaging screen names, among other exploits. He has yet to be charged for the AOL breaches but told Wired News on Monday that the AOL activity, which he began in 1997, was the "gateway drug" that emboldened him and other members of Defonic Crew to graduate to other hacking projects.
"If there was a security breach (at AOL), we were all a part of them.... That's how we all started," he said. "We all met up on AOL breaking into their crap. If it wasn't for AOL none of this (LexisNexis stuff) would have happened."
"Shasta," a hacker who knows Defonic Crew but isn't a suspect in the LexisNexis breach, said the success of the AOL breaches made Defonic Crew careless about not covering its tracks in LexisNexis.
"It made them feel invincible," he said. "And they weren't worried about getting caught."
They naturally are circumspect in the face of possible consequences.
"I really wish that I hadn't been able to get access to (the LexisNexis database)," said the 20-year-old, who lives in Rhode Island and goes by the name "Krazed." "Curiosity gets you in trouble."
....
"You start looking at an account that's been logged into 500 times and generated 9,000 reports, for example, that's a lot of information (to examine)," Sibley said. "I'm just saying it's not one group that's compromised LexisNexis. Their security is really bad. This isn't a situation where you're talking about needing an uberhacker to compromise (the system). Their passwords weren't as secure as your average porn site. I think it didn't take a genius to break them. Although I think the way the hackers did it was creative. We'll give them style points."
May 13, 2005
Penny-eating worms, and how crypto should be
Research on apotential SSH worm is reported by Bruce Schneier - this is academic work in advance of a threat, looking at the potential for its appearance in the future. Unusual! There is now optional protection available for the threat, as an option, so it will be interesting to see if this deploys as and when the threat arises.
Ping rites to say that he "recently started a weblog on usable security at http://usablesecurity.com/:
"I haven't seen any other blogs on the topic, so it seemed like a good idea to get one going. I invite you to read and comment on the entries there, and i hope you will find them interesting."
Great stuff. HCI/security is at the core of phishing. Which also brings us to an article about how the KDE people and the usability people eventually came to see eye to eye and learn respect for each other's strangenesses:
"When trying to set up a mail account with an OpenPGP key in KMail, you have to make settings in three different configuration modules. Users have problems understanding that. This is not a technical issue, because once the user discovers how it works he can set everything up. But to make the developers understand that users might have a problem with the workflow, you have to explain the context of usage and the way common users think."
Which brings me to something I've been meaning to shout about - when I (finally) got KDE 3.4 compiled and running, and started using Kmail (Thunderbird has too large a footprint) the GPG encryption feature just started working!
I'll say that again: encryption using my GPG Keys JUST STARTED WORKING!!! Outstanding! That's how encryption should be - and I don't know how they did it, but read the article for some clues.
It's not perfect - for example, the default is some hairbrained attachment scheme that nobody I know can read, so I have to remember each time to select "Inline (deprecated)" which is of course how it should be sent out for cross-platform independence. But it sure beats vi&cut&paste.
May 09, 2005
Threats are two a penny
Good story about a success at defending from a DDOS. As a company sprung out of it, this is obviously a marketing story, but it still gives a lot of good background into the DDOS world. Postini reports that phishing traffic is 45% down in April, over March. Also, viruses are down a bit. Valid email is 13% of messages.
Whoops - here's a wakeup - SSH has been attacked and was implicated in the Cisco source code heist:
Shortly after being stolen last May, a portion of the Cisco programming instructions appeared on a Russian Web site. With such information, sophisticated intruders would potentially be able to compromise security on router computers of Cisco customers running the affected programs.There is no evidence that such use has occurred. "Cisco believes that the improper publication of this information does not create increased risk to customers' networks," the company said last week.
(I'll bet they're regretting that statement in the post-Choicepoint world. Here's the details on SSH.)
The crucial element in the password thefts that provided access at Cisco and elsewhere was the intruder's use of a corrupted version of a standard software program, SSH. The program is used in many computer research centers for a variety of tasks, ranging from administration of remote computers to data transfer over the Internet.The intruder probed computers for vulnerabilities that allowed the installation of the corrupted program, known as a Trojan horse, in place of the legitimate program.
In many cases the corrupted program is distributed from a single computer and shared by tens or hundreds of users at a computing site, effectively making it possible for someone unleashing it to reel in large numbers of log-ins and passwords as they are entered.
Once passwords to the remote systems were obtained, an intruder could log in and use a variety of software "tool kits" to upgrade his privileges - known as gaining root access. That makes it possible to steal information and steal more passwords.
The operation took advantage of the vulnerability of Internet-connected computers whose security software had not been brought up to date.
In the Cisco case, the passwords to Cisco computers were sent from a compromised computer by a legitimate user unaware of the Trojan horse. The intruder captured the passwords and then used them to enter Cisco's computers and steal the programming instructions, according to the
security investigators.
Peversely this is good long expected news: it confirms that which we have always predicted, that when SSH is attacked it will be attacked around the system rather than the supposed weakness of the MITM. This is an economically rational attack; break in some other way, and replace a trusted tool with a trojan. Security experts may be wild-eyed zealots, but at least their attackers are economically rational.
In closing, cautionary tale of a security breaches misanalysed. Bob spotted this one:
Sherlock Holmes and Dr Watson go on a camping trip. After a good dinner and a bottle of wine, they retire for the night, and go to sleep.Some hours later, Holmes wakes up and nudges his faithful friend. "Watson, look up at the sky and tell me what you see."
"I see millions and millions of stars Holmes," replies Watson.
"And what do you deduce from that?"
Watson ponders for a minute.
"Well, astronomically, it tells me that there are millions of galaxies and potentially billions of planets. Astrologically, I observe that Saturn is in Leo. Logically, I deduce that the time is approximately a quarter past three. Meteorologically, I suspect that we will have a beautiful day tomorrow. Theologically, I can see that God is all powerful, and that we are a small and insignificant part of the universe. What does it tell you, Holmes?"
Holmes is silent for a moment and then says: "Watson you idiot, someone has stolen our tent!"
May 06, 2005
Damaged Pennies
Netcraft publishes the top phishing hosters - and puts Inktomi in pole position. Think class-action, damages, lack of due care, billion dollar losses ... we need more of this naming and shaming.
Rumours abound that Microsoft is about to be dragged into the security mess. I had thought (and wrote occasionally to effect) that the way phishing would move forward would be by class-action suits against software suppliers, following the lead of Lopez v. Bank of America ([1], [2]). But there is another route - that of regulators deciding to lean on the suppliers. Right now, that latter path is being explored in smoke-filled rooms, or at least that's what those who smoke say.
These two routes aren't exactly in competition, they are more symbiotic. Class-action suits often follow on the judgments of regulatory settlements, so much so that the evidence one side discovers is used by the other side to advance. In this way they work as a team.
Over on CACert, Duane alerts me to a blog that they run, and an emotional cry for help by an auditor from Coopers and Lybrand (now PriceWaterhouseCoopers). Like my own observations, the briefly named 'Gary' points out that CACert's checking procedures are as good or better than the others. He also breaks ranks and wiggles the finger at immoral and probably illegal practices at auditors in security work. I am not surprised, having heard stories that would make your faith in public auditors of security practices wilt and expire forever more. Basically, any *private* audit can be purchased and it costs double to write it yourself. Trust only what is published, and even then cast a skeptical eyebrow skywards.
Speaking of Microsoft and car wrecks to come, this factoid suggests that "25 car models run Microsoft software" ... unfortunately or perhaps luckily there is no reference.
In more damages of the other kind, RIAA File-Sharing Lawsuits Top 10,000 People Sued. In the Threats department: One-Third Of Companies Monitoring Email. Also, a nice discussion on fraud by fraudsters. A Newspaper interviews two fraudsters behind bars for what we now know as identity theft. Good background material on why and how easy.
AOL in Britain reports that one in 20 report that they have been phished. I find these sorts of surveys somewhat "phishy" given that if one in 20 of the population has been phished, we'd have rioting in the streets and politicians and phishers alike strung from lamposts. But, it's important to keep an eye on these datapoints as we want to know whether the status of phishing as primarily an "american disease" is likely to go global.
And in closing, a somewhat meanandering article that links Sarbanes-Oxley, IT and security products. It asks:
"But here is the fundamental question - has there ever been a pervasive and material financial fraud which has resulted directly or indirectly from a failure of an IT security control? Would IT controls have prevented or detected the frauds at Enron, WorldCom, Tyco, and the like?"
The author might be a closet financial cryptographer.
And, if you got this far, it is only fair to warn you that you've now lost 10 points of your IQ level. (Sorry, no URL for the following ...)
It's the technology, stupid
By Michael Horsnell in London
April 23, 2005
THE regular use of text messages and emails can lower the IQ more than twice as much as smoking marijuana. Psychologists have found that tapping away on a mobile phone or computer keypad or checking them for electronic messages temporarily knocks up to 10 points off the user's IQ.
This rate of decline in intelligence compares unfavourably with the four-point drop in IQ associated with smoking marijuana, according to British researchers, who have labelled the fleeting phenomenon of enhanced stupidity as "infomania".
Research on sleep deprivation suggests that the IQ drop caused by electronic obsession is also equivalent to a wakeful night.
The study, commissioned by technology company Hewlett Packard, concludes that infomania is mainly a problem for adult workers, especially men.
The noticeable drop in IQ is attributed to the constant distraction of "always on" technology, when employees should be concentrating on what they are paid to do. They lose concentration as their minds remain fixed in an almost permanent state of readiness to react to technology instead of focusing on the task at hand.
The brain also finds it hard to cope with juggling lots of tasks at once, reducing its overall effectiveness, the study has found. And while modern technology can have huge benefits, excessive use can be damaging not only to a person's mind, but also their social life.
Eighty volunteers took part in clinical trials on IQ deterioration and 1100 adults were interviewed.
Sixty-two per cent of people polled admitted that they were addicted to checking their email and text messages so assiduously that they scrutinised work-related ones even when at home or on holiday. Half said they always responded immediately to an email and 21 per cent would interrupt a meeting to do so.
Furthermore, infomania is having a negative effect on work colleagues, increasing stress and dissenting feelings. Nine out of 10 polled thought that colleagues who answered emails or messages during a face-to-face meeting were extremely rude. Yet one in three Britons believes that it is not only acceptable to do so, but actually diligent and efficient.
The effects on IQ were studied by Glenn Wilson, a University of London psychologist, as part of the research project.
"This is a very real and widespread phenomenon," he said. "We have found that infomania, if unchecked, will damage a worker's performance by reducing their mental sharpness."
The report suggests that firms that give employees gadgets and devices to help them keep in touch should also produce guidelines on use. These "best-practice tips" include turning devices off in meetings and using "dead time", such as travelling time, to read messages and check emails.
David Smith, commercial manager of Hewlett Packard, said: "The research suggests that we are in danger of being caught up in a 24-hour, always-on society.
"This is more worrying when you consider the potential impairment on performance and concentration for workers, and the consequent impact on businesses.
"Always-on technology has proven productivity benefits, but people need to use it responsibly. We know that technology makes us more effective, but we also know that misuse of technology can be counter-productive."
>From The Times of London in The Australian
April 27, 2005
Pennies on the CV
Allan Friedman took the scam conference issue more seriously and googled for it. To his surprise he discovered that it filled a real need - academics need line entries on their CVs of papers presented at conferences in order to meet their tenure targets. Is anyone shocked at this obvious need being filled? Market, meet incentives... incentives, market.
Also poking around on his site I found notes on FC05 for those that didn't go, and also FC04. Thanks Allan! I hope you got some mojitas in.
Sometimes it's hard to give credulity to the things you read in the press. Here's the story about how some Brits were arrested with $3 trillion of forged currency. I suspect that's more than the amount of USD notes out there in the first place, so it's only worth asking for amusement value how these guys got $3 trillion into the proverbial briefcase.
Another scam is being attacked in the US. The way this one works is that there are various stupid laws and regulations that allow non-profits to step in and deal in retail finance. Enterprising scammers set up these non-profits and take on the business that would previously been known as loan-sharking. They then either outsource (as intimated below) or they pay themselves huge salaries. The basic model here is "debt relief" where retail debts (like too many credit cards) have this odd clause: someone can step in, aggregate all your debts and force all lenders into keeping at bay. For a fee that is. Hopefully with a few cases more like this the legislators will realise the folly ("unintended consequences") of getting too tricksy with bankrupcy.
Posts have been slow here in FCland, and it isn't the spring weather. My laptop lost its screen; and 5 days later I'm still compiling KDE on the 7-year-old standby... thinkpads never die but there are lots of ways to drown them in mollasses. As soon as I get back onto graphical net, I intend to pursue 3 - three - contenders for a founding edition of FC++. I know who you are ;-)
(Oh, and late breaking rumours abound of a new project called Joe-E which is a <hush> rewrite of Java </hush> to be usefully secure. I can't wait, and hope we can round up the scalliwags who mucked it up last time and run them out of town. In another life I want to do the security, in this life I'll settle for talking to the guys who do.)
April 16, 2005
A Penny at a Time
Sarbanes-Oxley victims are counting pennies. They know, or they have been told, it will bring benefits. But at what costs? Audit costs seem anecdotally to be up by 50% or so. Honest injuns think it might not be worth the cost. Chiefs keep silent, it isn't worth their salary to rock the canoe. Interestingly, the article suggests that this year is a hump, and next year should be cheaper as the systems are in place.
Which reminds me of another set of victims counting cost - the Brits. For some reason they've noticed that it is now very difficult to open a bank account, which might have unintended consequences.
Martin Hall, chairman of the JMLSG editorial panel, said: 'We have taken a radical approach. The new guidance reflects the reality, that most customers are neither money launderers nor terrorists.
Over in certification land, the recent insider job in an Indian outsourcing firm is being ramped up by those who hate outsourcing. Another article points out:
" Ironically it shows the weakness of the certification system, which is supposed to guard against things like this. The centre in Pune was BS 7799- and CMM Level 5-certified, yet the fact that such a theft took place shows that such assurances probably arent worth that much."
It's just one cute data point, we'd needs a survey to really decide if that was statistically meaningful. Here's some more data points: The alleged #8 spammer in the world got 9 years in the slammer.
Let's work that out. If each spam costs a lost second to delete, then 3 million spams is worth a year. Nine years is worth 27 million spams. Now, if #8, a.k.a. Jeremy Jaynes sent a mailshot of a million a day, and he'd been doing it for a month, that's about right. An eye for an eye, a second for a spam. If however he had consumed say 70 spam-years, then that's a death sentance: 220 million spams means we lost a life somewhere, in the aggregate.
Looks like he got off lightly.
Meanwhile, some great figures are appearing from an e-crime conference where CEO from HSBC, spoke.
"The UK apparently leads the world in terms of 'bot nets', or collections of compromised computers that are rented out by criminal gangs. In March of 2004, German police uncovered a network of 476 hackers in 32 countries who had turned more than 11,000 computers into such 'zombies'. In September 2004 a Norwegian internet company shut down a bot-net controlling 10,000 machines. And SpamHaus estimates suggest 50,000 new zombie systems may be appearing each week."
And in the proportionality stakes, the unintended consequences of criminalising theft of IP strike home: one games manufacturer has complained to the FBI about several years of illegal selling of their game. By rights, the FBI ought to swoop in and bust the place up ...
I wonder if anyone has thought of making a game of strategy out of IP theft?
April 10, 2005
Penny Chat
I hadn't noticed this before but PGP's new beta version 9 of their product includes AIM chat protection. I guess this means that even though PGP Inc people don't agree with me that email is dying, a hedge isn't a bad thing.
Mozilla security is back in the news again with a $2,500 bounty for Firefox flaws. I think this is a good idea. Research I'm working on indicates a dramatic need to improve information (as opposed to acquiring information from asymmetrically informed parties, which I reject) and this is one way to do it.
Speaking of paying for stuff, it seems that the top price for your social security number (if you are an american) is $45. That sounds high to me, there are obviously going to be deals for bulk work.
It's $35 at www.secret-info.com. It's $45 at www.Iinfosearch.com, where users can also sign up for a report containing an individual's credit-card charges, as well as an e-mail with other "tips, secrets & spy info!" The Web site Gum-shoes.com promises that "if the information is out there, our licensed investigators can find it.""The current system has the worst of all worlds," Solove said. "Anyone can easily find it [the Social Security number] out . . . It's used everywhere, and it's really hard to change if it falls in the wrong hands. How could you come up with a worse system?"
Yes, I'd agree. In fact if we all sat down and tried to design a worse system, I'm not sure we could. Why is that?
An unusual claim: are people naturally doing mental double entry bookkeeping? An article suggests that they are. I'm not so sure I'd go that far, but it is food for thought. Note that the article does not list any primary research, and the site for the interviewee has older papers listed only:
In closing, more research saying "you should buy our 2-factor doobelackie."
Published: 01/04/2005 00:41:00Banks urged to act on Net security fears
Banks must act "urgently" to tackle Net user security fears if they are to
retain and attract customers to cheaper online channels says Forrester
Research.In a survey of more than 22,000 Europeans, Forrester found that just 30% of
Internet users are confident of the security of personal financial
information, like credit and debit card numbers, when used to make
transactions online. Two-fifths of the European Net users who don't use
online banking say they don't because they worry about security.Benjamin Ensor, senior analyst, financial services at Forrester says:
"Consumers' deep-seated security fears remain one of the biggest barriers to
online banking use in Europe, particularly in countries like Italy, France,
and the UK, where two-factor online banking authentication is rare or
unknown. The more confidence Net users have in security, the more likely
they are to bank online."The analyst group says that banks should look to educate Net users about
security precautions, not let usability fears compromise security, deploy or
strengthen two-factor authentication "urgently", and collaborate rather than
compete on security.¿ Finextra Research 2005
It is amazing what research you can buy in an open market.
April 05, 2005
Pennygate
Jim posts his proposal for fixing email crypto.
Rumours abound about trouble in Wall Street based on derivatives. Citibank is drowning in unmatched derivative positions, and their plan is to net it all and write off the rest. No, they ain't saying how much that means, but apparently their market cap and their bond ratings are of much interest. As are General Motors' numbers. Meanwhile the AIG scandal broadens and it looks like Berkshire-Hathaway, famed vehicle of Warren Buffet, is likely to be dragged in for more than questions.
Can we say one word, please? Settlement.
Elliot Spitzer's office in New York is again in action, and we now have to just accept that the AG's office of New York is one of the top tier regulators in the US, alongside the Fed, the SEC and the others. Elliot Spitzer is somewhat hated on the (Wall) Street, but he has a habit of picking real targets, unlike his predecessor (who was truly despised). Spitzer is loved by the man in the (main) street, so it's likely there are shoes in his size waiting in either the Governor's office or the Mayor's office.
Stefan points out that the Department of Homeland Security and Liberty Alliance are both engaged in the same form of doublespeak, using the names of one thing they are not doing to describe exactly the opposite. I've always wondered why Liberty Alliance came across as the worst form of snake oil and now I know - because it is. Their psuedonyms are centrally created and controlled!
I've always been suspicious of the Liberty Alliance, as their name stinks. It sits in the same bucket of snake oil as "Patriot Act" and indicates that they are intentionally trying to dupe people. How dumb do they think we are?
And in more scandal news, Bob reports that Dateline is to air the Stockgate scandal on the 10th April.
A good article on the impending VoIP telemarketing boom. The normally relaxed Cubicle says this ain't gonna happen, but I've already seen it in action. It'll happen, but maybe not as the reported in that article.
And in Moscow, the central bank got embarrassed when copies of its transaction database were advertised in the press. Even worse, the price started at $2000 and dropped down to $800 for about a year and a half's worth! Talk about a poke in the eye with a burnt stick.
Biggest transaction: 2.96 billion rubles for some bonds. Should have used SOX!
And, just in: Adam points at ElReg's reporting of Microsoft recruiting security engineers. Definately worth a read if you are trying to figure out what Microsoft thinks security means.
March 27, 2005
A penny here...
The shocking truth - spam works!! - is revealed in a breathtaking survey by the Radicati group. Jokes about lack of economic nounce aside, the numbers in there are quite interesting: 10% of respondents have purchased products advertised in spam.
In contrast to that, a well written case study that discusses how a seemingly innocent blunder cost a legal practice $100k in down time. It is issues like these that make the risks approach to security all the more incisive.
More shocking truths - Microsoft pays for independent reports that slam their opposition's security. The only reason I bring this obviosity up is because it's going to be happening to a browser near you, in the second half of this year.
Russian payments company WebMoney has been hit for frauds of $1.5m. It looks like that got the (a) guy, but not clear on whether the funds are lost or not.
Good blog post that simply lists the 5 Choicepoint shareholder lawsuits.
FUDWatchers Freedom is Slavery and Stupid Security spot another case where Sandia Labs looks to do more damage to society than any terrorist ever dreamed of. It's thinking like this that leads to graver vulnerabilities, under the facade of yet more security solutions that earn big bucks but don't work. No thanks.
Phishing gets some respect from the academic world at a workshop in Rutgers University, New Jersey, USA. 14-15 April.
In closing, a few notes on FC admin. I have adopted Adam's lead and created a Pennies category for little snippets that come my way. Pennies are just my way of clearing down the desktop, sorry about that.
Also, some of them may not be mailed out, this is generally something that I do if they are readable, but once the links get deeply embedded for website clicking on the blog, they become unreadable.
Another point: the mail list is manual. If you want off, or on, or any points in between, just reply and I shall obey. Privacy notice: I don't have time to collect or datamine your identity.
March 22, 2005
For a few Pennies more...
Maybe there's hope for Microsoft yet .. they are reported as saying nothing at all about IE 7.0 security upgrades for phishing.
There's no hope for Sun.
They recently announced yet another set of licences (1 2 3) still lumbered with the core requirement of making it difficult to share Java. Lack of shareability makes porting the language to platforms a Sisyphean task. As open source volunteers slave at the onerous and unpaid task of getting compilers bootstrapped and working, they cannot release their binary results; so each unpaid volunteer is locked into pushing their own stone up the hill until somone pays the Sun Gods to let them join together and push up one stone.
The time taken to push Java from new release source through installed binary and then start getting some packages out to the users is about the same time as the gap between major releases. There is rarely a time where the users on open source platforms feel the language is stable, hardly a reward for adoption. The stone rolls down again, and Sun are trapped in the eternal punishment of their "Write once, Run twice" arrogance.
Over at Mozilla, the luster of the unknown is rapidly tarnishing off Firefox. Here's an article by someone who bothered to go looking at the security. Conclusion? More of the same.
Following on from the Choicepoint debacle, two of America's banking regulators, the FDIC and the OCC - have decided that financial institutions must warn customers of security breaches [1]. t seems that 6% of America's bank customers have already sent their banks a similar message.
March 03, 2005
Short ones...
Hop on a plane, land, and discover Adam has posted 13 blog entries, including one that asks for more topics! Congrats on 500 posts! He posts on some testimony: " the only part of our national security apparatus that actually prevented casualties on 9/11 was the citizenry." More on security measurements ("fundamentally flawed"). Tons or stuff on Choicepoint.
Axel talks about what it means to be a security professional. Yes, there are some media stars out there, but remember "don't believe Vendor pitches." Sounds like something I would write.
Scott points at an article on the inside story of how plastic payments are battled over in Australia. Sadly, the article requires yet another subscription to yet another newspaper that you only read once and they have your data for ever. No thanks.
Stefan does some critical analysis of psuedonyms; very welcome, there is an absence of good stuff on this. A must read for me, so remind me please... Meanwhile, he comments that laws won't help identity theft, but "Schwarzeneggers administration ... should point legal fingers ... at organizations that hold, distribute, and make consumer-impacting decisions based on identity information..." It is correct to recognise that the problem lies fundamentally with using the identity as the "hitching post" for animals in the future, but finger pointing isn't going to help. (It's a case of the One True Number.) More on that later, when I've got my draft expose on finger pointing in reasonable shape.